Nick Gascon
@nickgascon
- 4 Followers
- 83 Following
- 17 Posts
all these new generation copy-on-write filesystems, and yet no one has been brave enough to name theirs simply "cowfs". then they could call the package containing its mkfs, fsck, etc. "cowtools"
Pick the best fallacy
Sunk Cost has been my favorite since 1982
Proof by Assertion is best
Why y'all hate Strawman so much
I just heard about Recency Bias
If you don't vote Ad Hominem you're ugly
Any fallacy fan knows No True Scotsman is best
God told me Appeal to Authority is his favorite
"Vote for False Attribution" - Abraham Lincoln
The best is Circular Argument because it's awesome
Category Error is the prettiest fallacy
You said Tu Quoque so I did too
C'mon vote Bandwagon everyone's doing it
Vote Slippery Slope, next thing you're doing drugs
I like turtles and also Non Sequitur Fallacies
If Appeal to Probability can be chosen then it is
Motte-and-Bailey is best, but I meant kinda good
These are all bad and wrong, vote Fallacy Fallacy
Poll ended at .
Tip to get the most out of #BlackFriday:
Show up early and snag a parking spot near the entrance, then stay in your car the whole time with your reverse lights on.
♥️
Why eat turkeys, when you could have this?! 🦃
I am possibly over tired because I cannot stop laughing.
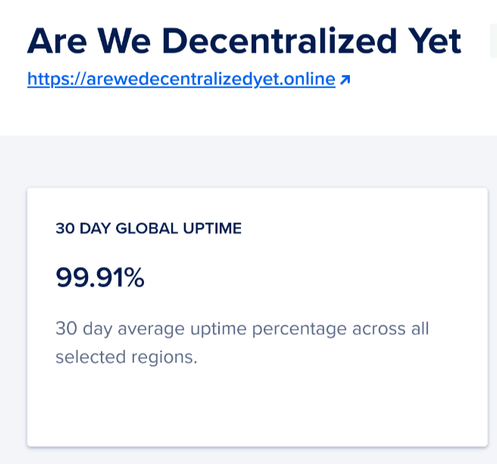
MFW the website I run on a raspberry pi sitting in my living room has better uptime than two of the planet's largest cloud providers
https://mltshp.com/p/1R4Z3 “Antifa Batman”
Ok! Figured out a simple way to pull *local* hashes out of Canon iR-ADV (imageRunner) printers.
The goal of this "hack" is to use access to a printer to gain further credentials that can be used to pivot further into the network.
This is a separate "attack" than pulling the LDAP domain credentials out of the printer.
So you *start* with administrative access to the printer - say through the use of default credentials (Most iR-ADV printers have the default credentials of User: Administrator (with a capital A) and Pass: 7654321 ).
Once logged into the printer with admin credentials, go to "Authentication Management > User Management > Export"
Export the file into an Excel spreadsheet.
In the column "sdl_digest" you'll see the password hash. The hash is "Raw-MD5" with no salt. So load that into your favorite hash cracker and have fun.
Note, this account is a LOCAL account on the printer. This only works if some printer admin went in and created a new local account. Not all printers have local accounts. There is no reason for this account to give you any access into anything else besides the printer that you ALREADY HAVE ADMIN access to.
Buuuuuuut..... folks often set up their account to mimic their domain accounts. So the password is often the same as their domain accounts (or was the same two years ago... so take the time since creation, divide by 90 days, and add that resultant number to the end of the password you cracked).
One of my all-time weirdest Wordles
Wordle 950 5/6
⬜⬜⬜⬜⬜
⬜⬜⬜⬜⬜
⬜⬜⬜⬜⬜
🟩🟩🟩⬜⬜
🟩🟩🟩🟩🟩
The effectively costless nature of Internet traffic means you need to throw out various assumptions about “attacks.”
There’s no way to make testing Walmart Theft Prevention free. On the Internet, usually all it takes is denying the connection because it’s to an invalid place.
There’s no way to make testing Walmart Theft Prevention free. On the Internet, usually all it takes is denying the connection because it’s to an invalid place.