Chrome decided to derestrict an interesting bug from @jann from 7 years ago. Android applications with the READ_EXTERNAL_STORAGE permission were able to steal CSRF tokens by forcing the browser to save arbitrary web pages to disk and then read these files from the Downloads folder.
https://bugs.chromium.org/p/chromium/issues/detail?id=587956
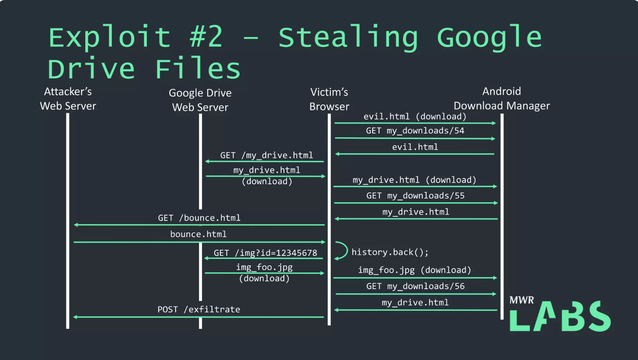
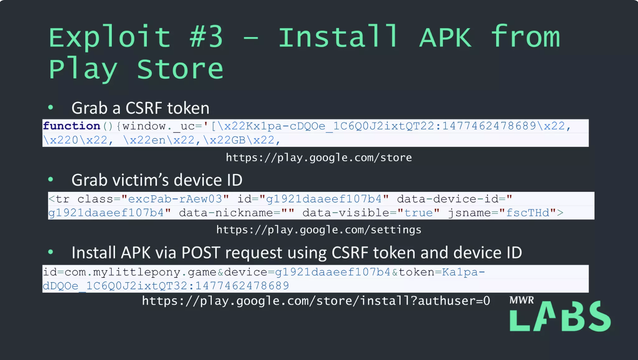
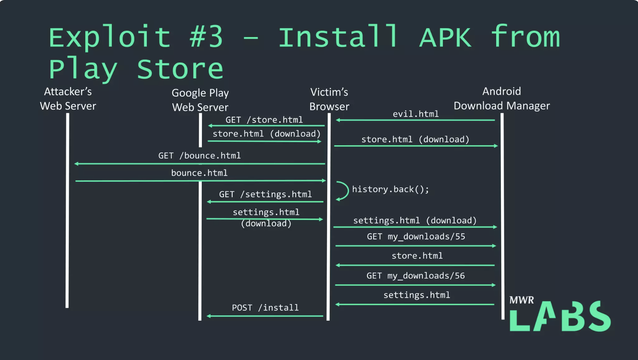
Coincidentally, some 6 months later, Rob M and I paired the same bug with a SOP bypass at #Pwn2Own 2016 to exfiltrate Google Drive files and remotely install an APK via Google Play's web front-end.