Matthijs R. Koot
- 530 Followers
- 51 Following
- 62 Posts
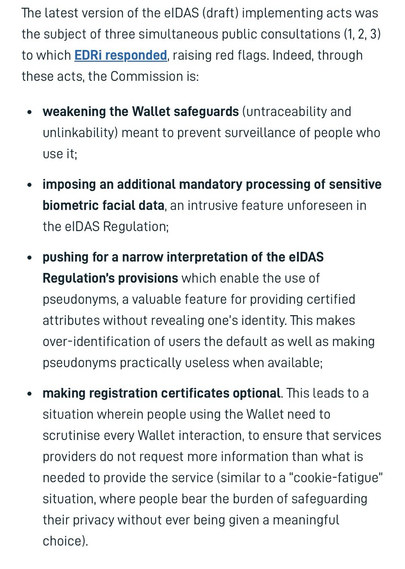
What WeChat Knows: Pervasive First-Party Tracking in a Billion-User Super-App Ecosystem (August 2025) https://petsymposium.org/popets/2025/popets-2025-0163.php
By Wang et al., presented at PET Symposium 2025. Open Access.
Artifacts available at The Citizen Lab’s GitHub: https://github.com/citizenlab/wechat-security-report/tree/artifact
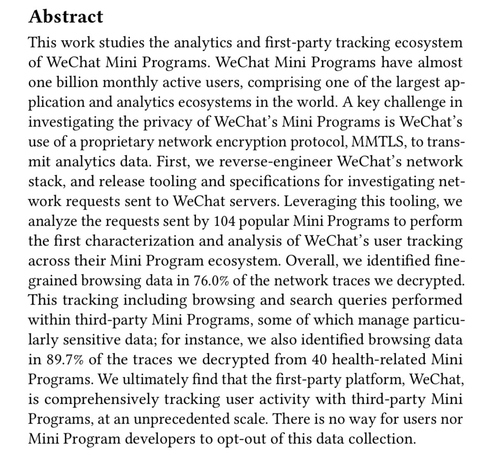
Disrupted, Throttled, and Blocked: State Censorship, Control, and Increasing Isolation of Internet Users in Russia (30 July 2025) https://www.hrw.org/news/2025/07/30/russia-internet-blocking-disruptions-and-increasing-isolation
Full report (.pdf, 69 pages) https://www.hrw.org/sites/default/files/media_2025/07/russia0725%20web.pdf
Full report (web): https://www.hrw.org/report/2025/07/30/disrupted-throttled-and-blocked/state-censorship-control-and-increasing-isolation
Taiwan Bounty: PRC Cross-Agency Operations Target Taiwanese Military Personnel (25 July 2025) https://jamestown.org/program/taiwan-bounty-prc-cross-agency-operations-target-taiwanese-military-personnel/
'[...] the Guangzhou Public Security Bureau recently issued a “wanted” notice offering a reward for information leading to the apprehension of 20 retired and active personnel in Taiwan’s Information, Communication, and Electronic Force Command (ICEFCOM). [...]'
Commercially sourced intelligence: friend or foe? (2024, Open Access) https://doi.org/10.1080/02684527.2024.2437955
By Vivi Ringnes Berrefjord and Tor Erling Bjørstad, published online December 2024 in Intelligence and National Security, Volume 40, Issue 3.
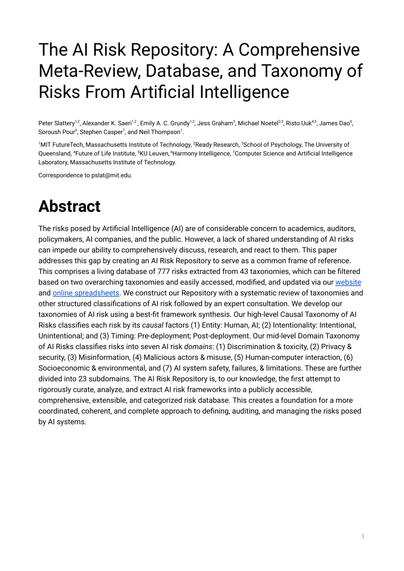
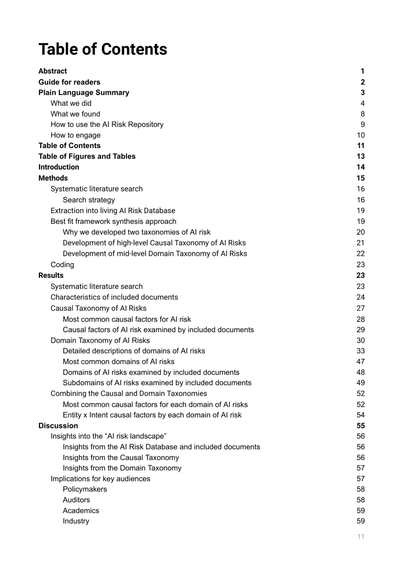
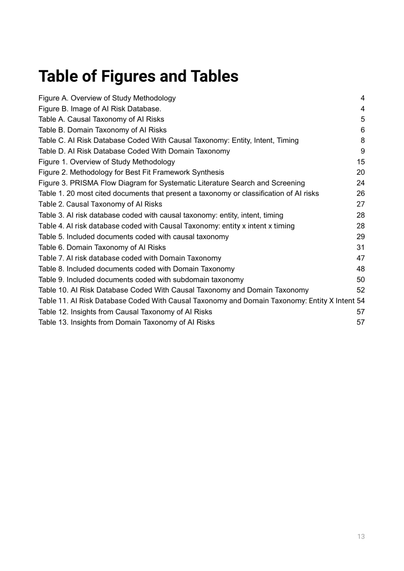
AI Risk Repository (2024) https://airisk.mit.edu/ at MIT
A comprehensive living database of over 700 AI risks categorized by their cause and risk domain.
More details in this 79-page preprint (1.9MB .pdf): https://cdn.prod.website-files.com/669550d38372f33552d2516e/66bc918b580467717e194940_The%20AI%20Risk%20Repository_13_8_2024.pdf
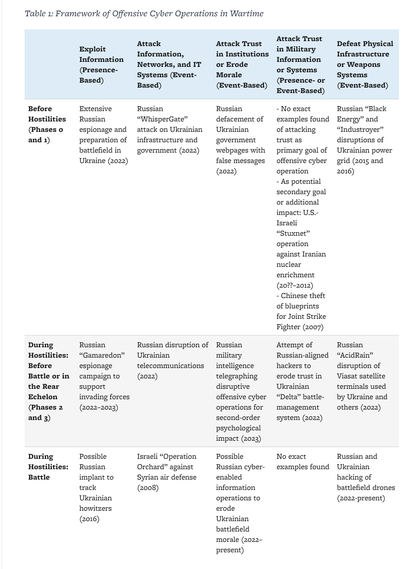
Cyber Effects in Warfare: Categorizing the Where, What, and Why (Aug 2024) https://tnsr.org/2024/08/cyber-effects-in-warfare-categorizing-the-where-what-and-why/
By Jason Healey. Published in Texas Nat'l Security Review, Vol 7, Issue 4, Fall 2024.
Paper introduces a novel analytical framework to assess offensive cyber operations based on the circumstances of their use across the different phases of war, from shaping operations prior to the conflict to the actual battlefield.
Cyber Effects in Warfare: Categorizing the Where, What, and Why - Texas National Security Review
For decades, military practitioners and academics have come up with theories, evidence, and examples that indicate that offensive cyber operations might revolutionize modern warfare. Others have made an equally impressive case that refutes that such operations would even be relevant, making it hard to reach any definite conclusions. This paper introduces a novel analytical framework to assess offensive cyber operations based on the circumstances of their use across the different phases of war, from shaping operations prior to the conflict to the actual battlefield. This framework substantially simplifies the key questions of practitioners and academics in order to pose the more direct question: Where, when, and how might offensive cyber operations affect warfare outcomes, both today and in the future?
Commercial Enablers of China’s Cyber-Intelligence and Information Operations (2024) https://digitalcommons.usf.edu/mca/vol7/iss1/1/
Published in Military Cyber Affairs, Vol. 7, Issue 1.
Direct link to paper (0.5MB .pdf, 12 pages) https://digitalcommons.usf.edu/cgi/viewcontent.cgi?article=1106&context=mca
Commercial Enablers of China’s Cyber-Intelligence and Information Operations
In a globally commercialized information environment, China uses evolving commercial enabler networks to position and project its goals. They do this through cyber, intelligence, and information operations. This paper breaks down the types of commercial enablers and how they are used operationally. It will also address the CCP's strategy to gather and influence foreign and domestic populations throughout cyberspace. Finally, we conclude with recommendations for mitigating the influence of PRC commercial enablers.
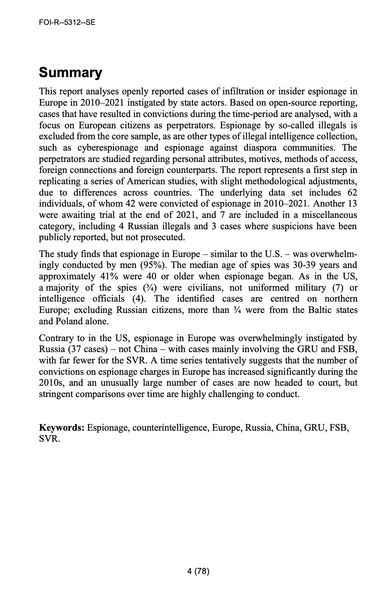
Espionage by Europeans 2010–2021. A Preliminary Review of Court Cases (May 2022) https://foi.se/en/foi/news-and-pressroom/news/2022-05-16-threat-of-spies-is-increasing-in-europe.html
Direct link to report (1.2MB .pdf, 80pp) https://foi.se/rest-api/report/FOI-R--5312--SE
Commissioned by the Swedish Security Service and Swedish Armed Forces. Study covers 62 individuals of whom 42 have been convicted.
Summary: see pic.
Audit of the FBI's National Security Undercover Operations (13MB .pdf, December 2022, 45pp): https://oig.justice.gov/sites/default/files/reports/23-012.pdf
Report from the U.S. DOJ Inspector General.
It makes 10 recommendations to improve how the FBI manages its NatSec Undercover Operations (UCO) program.