| Country | US |
| Domain name (don't click) | https://mn0.us/ |
| RFC 8509 (DNS chaos) | https://root-key-sentinel-not-ta-46211.mn-dns.monster/ |
Matt Nordhoff
- 155 Followers
- 126 Following
- 2.8K Posts
https://en.wikipedia.org/wiki/Npm_left-pad_incident
Thankfully, we've completely solved software supply chains in the years since.
So America is threatening to obliterate the entire energy infrastructure of a country of 90 million people, which would be the greatest disaster in human history, like, tomorrow.
Iran is threatening to retaliate by destroying further fossil fuel infrastructure, which, if they had much success, would be the greatest disaster in human history.
And almost everyone in America is acting like everything is fucking normal!
The Internet Last Week
* IETF 125
https://www.ietf.org/meeting/125/
* Cuba power outage effects
https://noc.social/@cloudflareradar/116240190351546459
https://mastodon.social/@IODA/116246041272623316
https://infosec.exchange/@dougmadory/116240466331483809
https://mastodon.social/@netblocks/116240861464667713
* IoT DDoS botnets disrupted
https://www.justice.gov/usao-ak/pr/authorities-disrupt-worlds-largest-iot-ddos-botnets-responsible-record-breaking-attacks
* Unallocated IP4 /13 announced
https://infosec.exchange/@spamhaus/116250561577999852
https://bgp.he.net/net/102.224.0.0/13
https://stat.ripe.net/widget/routing-history#resource=102.224.0.0/13&starttime=2026-03-15
* CAs must perform DNSSEC validation
https://cabforum.org/2025/06/18/ballot-sc-085v2-require-validation-of-dnssec-when-present-for-caa-and-dcv-lookups/
https://infosec.exchange/@mnordhoff/116240122433847371
Conspiracy theory: AWS S3 account regional namespaces help NSA map social graphs through DNS/TLS SNI (by including the account ID in the hostname).
https://aws.amazon.com/about-aws/whats-new/2026/03/amazon-s3-account-regional-namespaces/
The open source vulnerability scanner trivy has experienced a *second* security incident: a compromised release (v0.69.4) was published to the trivy repository.
https://www.stepsecurity.io/blog/trivy-compromised-a-second-time---malicious-v0-69-4-release
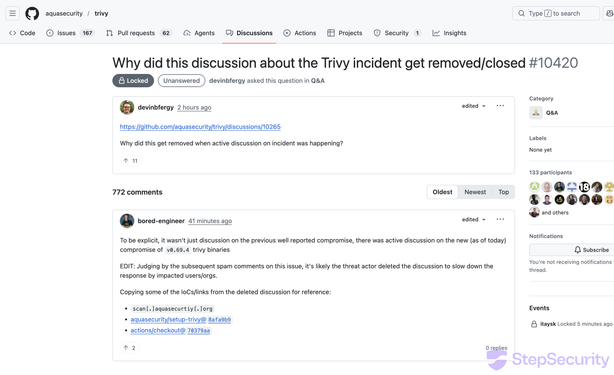
Trivy Compromised a Second Time - Malicious v0.69.4 Release, aquasecurity/setup-trivy, aquasecurity/trivy-action GitHub Actions Compromised - StepSecurity
On March 19, 2026, trivy — a widely used open source vulnerability scanner maintained by Aqua Security — experienced a second security incident. Three weeks after the hackerbot-claw incident on February 28 that resulted in a repository takeover, a new compromised release (v0.69.4) was published to the trivy repository. The original incident disclosure discussion (#10265) was also deleted during this period, and version tags on the aquasecurity/setup-trivy GitHub Action were removed. Trivy maintainers deleted the v0.69.4 tag and Homebrew downgraded to v0.69.3. The following is a factual account of what we observed through public GitHub data.
https://www.bbc.com/news/technology-35082344
<looks at Supermicro news>
So basically they got two out of three fall guys in a scheme that every executive knew about and NV most absolutely knew about 100%. One hundred percent NV had full knowledge. SXM parts do not just 'not show up' at customers. It also VERY much explains E&Y refusing to sign off and NV being okay with BDO USA (86% of their audits were deficient last year.)
cc @davidgerard