https://github.com/matteyeux/coruna
matteyeux
- 374 Followers
- 54 Following
- 122 Posts
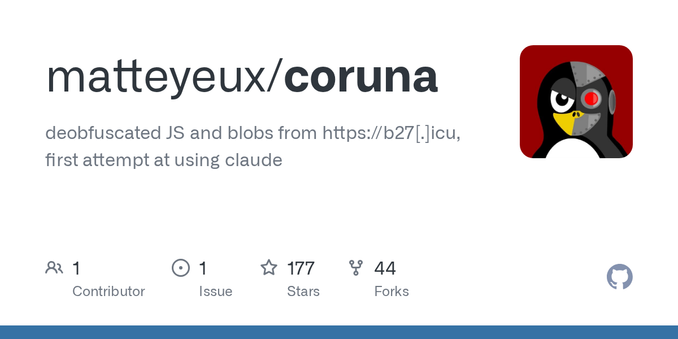
After playing a bit with the coruna exploit chain, I dumped the kernel exploit and one of the implants in powerd
https://github.com/matteyeux/coruna
https://github.com/matteyeux/coruna
I played a bit with Claude to deobfuscate the javascript code from the Coruna exploit chain, I was able to recover the implant and some ARM64 shellcode
Apple providing virtual iPhone could have reduced Corellium’s value as a company providing virtual iPhones and SEP stuff as an upsale.
Luckily it was acquired by Cellebrite before that happened.
Luckily it was acquired by Cellebrite before that happened.
Finaly got some time to play with vphone600 VM, now wen eta official apple support cuz I don't want to lower the security of my main laptop
Now that this guy from Trenchant has been convicted, I wonder whether Trenchant reported the stolen bugs to the vendors or if they’re still being used. Maybe OpZero will report them 😬
I suspect that Apple will provide virtual iPhones for security research this year (2026)
Some customer at the Apple Store left her Apple Watch she just bought on one of tables.
Told the guys in red about it and they offered me the smart folio with the iPad Air I just bought for being honest
Told the guys in red about it and they offered me the smart folio with the iPad Air I just bought for being honest
It's been a long time since I published a write-up, so...
Here's my little article about log strings obfuscation in modern iBoot and 2 methods I found to (partially) deobfuscate them
Read on your own risk!
🧐
Apple added new mitigations to iOS: SPTM, TXM, and Exclaves. Even in the case of a kernel compromise, various components stay protected. You can read about more technical details in Moritz' thesis: https://arxiv.org/abs/2510.09272

Modern iOS Security Features -- A Deep Dive into SPTM, TXM, and Exclaves
The XNU kernel is the basis of Apple's operating systems. Although labeled as a hybrid kernel, it is found to generally operate in a monolithic manner by defining a single privileged trust zone in which all system functionality resides. This has security implications, as a kernel compromise has immediate and significant effects on the entire system. Over the past few years, Apple has taken steps towards a more compartmentalized kernel architecture and a more microkernel-like design. To date, there has been no scientific discussion of SPTM and related security mechanisms. Therefore, the understanding of the system and the underlying security mechanisms is minimal. In this paper, we provide a comprehensive analysis of new security mechanisms and their interplay, and create the first conclusive writeup considering all current mitigations. SPTM acts as the sole authority regarding memory retyping. Our analysis reveals that, through SPTM domains based on frame retyping and memory mapping rule sets, SPTM introduces domains of trust into the system, effectively gapping different functionalities from one another. Gapped functionality includes the TXM, responsible for code signing and entitlement verification. We further demonstrate how this introduction lays the groundwork for the most recent security feature of Exclaves, and conduct an in-depth analysis of its communication mechanisms. We discover multifold ways of communication, most notably xnuproxy as a secure world request handler, and the Tightbeam IPC framework. The architecture changes are found to increase system security, with key and sensitive components being moved out of XNU's direct reach. This also provides additional security guarantees in the event of a kernel compromise, which is no longer an immediate threat at the highest trust level.