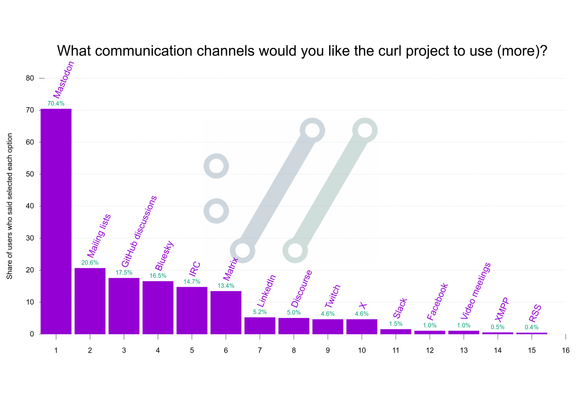
#curl user survey 2025 respondents like Mastodon:
Markus Wall
@markuswall
- 3 Followers
- 23 Following
- 5 Posts
Now disclosed: https://hackerone.com/reports/3230082
curl disclosed on HackerOne: Stack-based Buffer Overflow in TELNET...
**Title:** Stack-based Buffer Overflow in TELNET NEW_ENV Option Handling **Vulnerability Description:** **Summary:** A stack-based buffer overflow vulnerability exists in the `libcurl` TELNET handler. When `libcurl` connects to a malicious TELNET server, the server can trigger an overflow by sending a `NEW_ENVIRON SEND` request. This causes the client to construct a response that overwrites...
Sent a pull request to Audacity fixing a crash bug I'd been running into frequently. The cause was an out-of-bounds memmove. Classic C++ areas.
Anyway I got a fucking copilot review on my PR which left two comments, both completely wrong, one of which suggesting I reintroduce the out of bounds memory access. I'm furious!
Maybe it’s just me, but I’d much rather have an entire undocumented immigrant family with two happy trans kids living right next door to me than a white supremacist or a racist MAGA lunatic any day of the week.