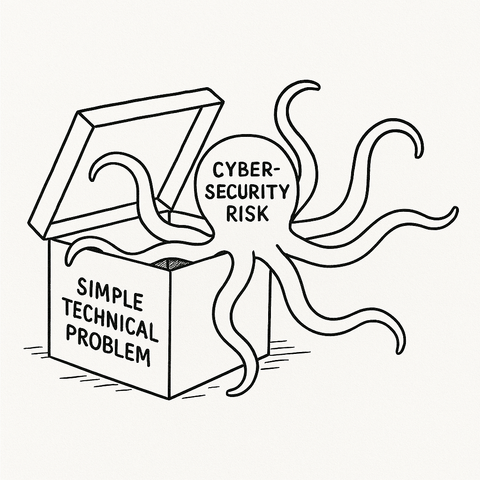
Ever been tempted to call people "stupid users" because they make a basic security or technology mistake?
I would advise against saying this and encourage you to change your thinking patterns. We need to respect the skills and knowledge of other professionals and remember that their basic skills and our basic skills are very different.
I know a lot about cybersecurity, but you don't want me to do 'basic' medical tasks like finding a vein in your arm to inject medicine, designing a 'simple' bridge for people to drive over, mixing a 'simple' chemical formula, or any number of other 'basic' tasks in a different profession.
If we think people should have basic cybersecurity knowledge (and we need them to!), we must take the time to talk to them in _their_ language.
We need to explain things by making analogies to similar common things they already know (fire prevention, kids safety, etc.) or professional things they already know (safety briefings in the petroleum industry, liability in the legal industry, etc.) so its clear and easy to them.
We must respect other professions and professionals the way we want to be respected as cybersecurity professionals. We are just people trying to do our jobs and so are they.