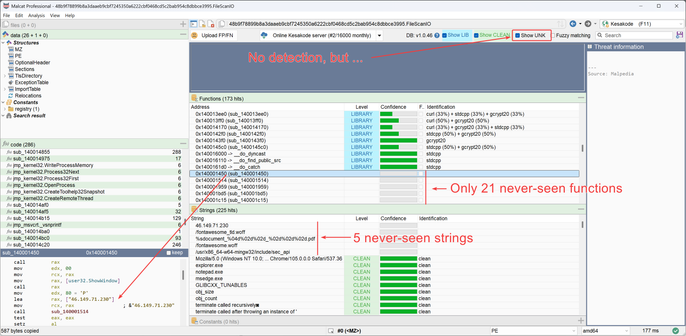
In Malcat, hitting <Ctrl+M> will start the in-GUI MCP server (works in free version too). You can then interact with the current analysis using your LLM of choice.
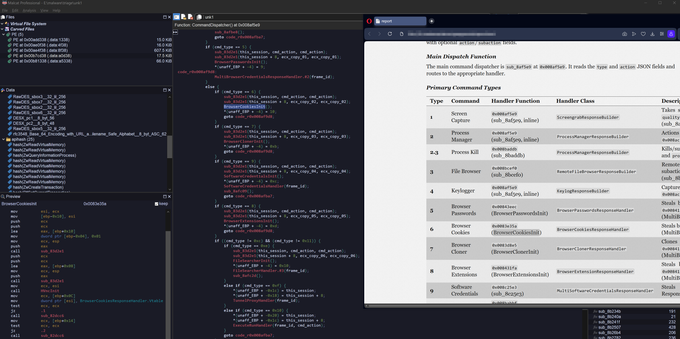
Here I renamed functions and variables of the C2 dispatcher function for an unknown malware: