A Race Within A Race: Exploiting CVE-2025-38617 in Linux Packet Sockets
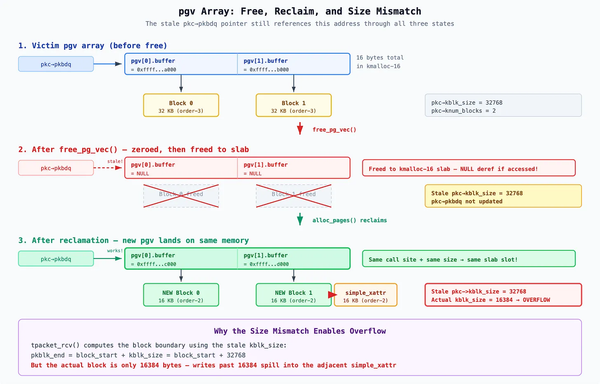
Excellent article by Quang Le about exploiting CVE-2025-38617 — a race condition that leads to a use-after-free in the packet sockets implementation.
The implemented exploit was used to pwn the kernelCTF mitigation-v4-6.6 instance. The exploit bypasses CONFIG_RANDOM_KMALLOC_CACHES and CONFIG_SLAB_VIRTUAL.
Article: https://blog.calif.io/p/a-race-within-a-race-exploiting-cve
Exploit: https://github.com/google/security-research/pull/339