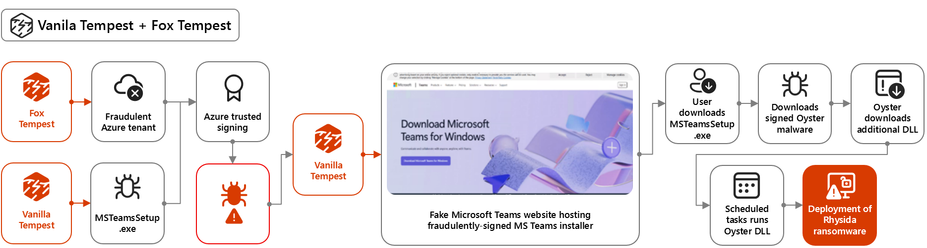
NEW: Microsoft has cracked down on Fox Tempest, a cyber threat actor that fueled Rhysida ransomware attacks.
It is now working with the FBI and @Europol to uncover the identity of people behind the group.
https://www.infosecurity-magazine.com/news/microsoft-takes-down-fox-tempest/