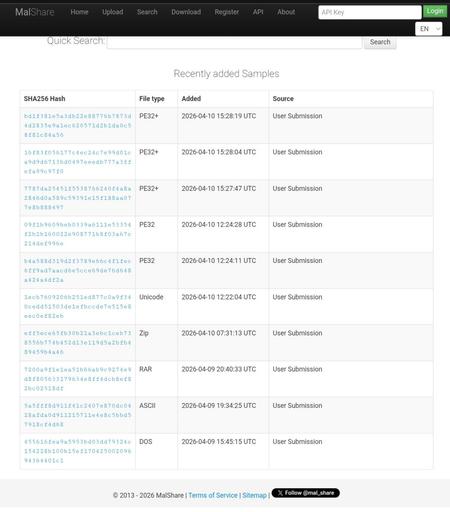
I think this wasn't mentioned on the Fediverse yet, so here we go: https://malshare.com is back up! If you've never heard of it: It's an openly developed and cost-free malware repository. As a resarcher, you can register an account and upload and download malware samples to share with other researchers. You only need an email address (feel free to use a throw-away). This sadly became necesarry btw to avoid abuse.
Anyway, we've been hard at work to discuss scope (and reduce it), did some spring cleaning, and automate as much as possible.
A couple of changes:
* CI/CD via github actions
* got rid of YARA scanning
* allowed URL submissions
* got the daily digest working again
Esp. not scanning with YARA anymore was a hard decision. Because without that, it's really just SHA256s. But it's surprisingly hard to run YARA at scale. And in the end, we figured: before there's no MalShare, let's have one without YARA.
We also centralized all issue tracking on https://github.com/Malshare/MalShare/issues. There were issues over 4 years old. We've addressed a couple and the plan is to not let it come to this in the future. Speaking of: please reach out if you want to get involved, we are not that many people and can use any help. There's also donation options to cover hosting cost (we have a lot of malware...).