| Github | https://github.com/jipegit |
| Keybase | https://jipe_.keybase.pub/mastodon.html |
| https://twitter.com/jipe_ |
Jipe 
- 207 Followers
- 179 Following
- 106 Posts
🕷️Two weeks ago I published a blog post on ALPHA SPIDER affiliates TTPs. This blog post highlights various and never publicly disclosed techniques used by several of their affiliates to:
- gain initial access;
- achieve persistence;
- obtain credentials;
- evade defenses;
- exfiltrate data.
Even if ALPHA SPIDER recently decided to shutdown their RaaS platform -in what looks like an exit scam to defraud their own partners-, their affiliates will likely just move to another RaaS and continue running their criminal operations.
« Sharing is caring », so do not hesitate to have a look at the blog post to leverage shared insights from the frontline to improve your threat detection capabilities and keep your network secure from destructive attacks! https://www.crowdstrike.com/blog/anatomy-of-alpha-spider-ransomware/
L'association #CECyF propose un serveur Mastodon, ouvert à tous les membres de la communauté de la réponse aux incidents et de l'investigation numérique, pour permettre d'explorer le #Fédivers en toute confiance.
Les inscriptions sont modérées pour éviter les abus de pseudonymes et conserver un caractère thématique (personnes connues de la communauté, ayant participé à la conférence CoRIIN ou travaillant chez un membre de l'asso).
Le serveur est accessible à l'adresse: https://riin.fr/
Developers of scam apps continue to use the same techniques to bypass App Store review, switching a pointer to interface code with a change to the server they fetch web code from. We found one fraud app used the same source as a previously discovered and reported app.
For more details see our full report here: https://news.sophos.com/en-us/2023/08/02/sha-zhu-pan-scam-uses-ai-chat-to-target-iphone-and-android-users/
I'm curious how many folks on Mastodon still use Twitter/X.
Boosts appreciated so I can get a better sense.
I've left Twitter completely.
I still use Twitter.
I was never on Twitter.
Predictable yet still fascinating metrics around the decline of Twitter usage by #infosec professionals..
we saw a weekday daily tweet count drop from the 1,272 pre-Elon average to just 333 tweets a day, which is about a 74% drop in weekday tweets
Warning to all MOVEit victims.
Clop is using a BlackCat tactic and created new URLs for MOVEit victims including Price Waterhouse Coopers.
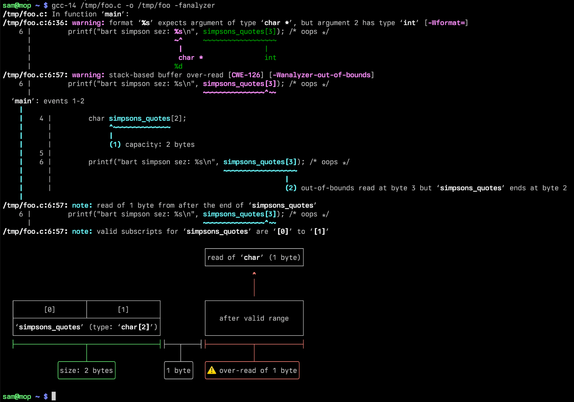
GCC 14 is still in development, but it has a wonderful new feature in its static analyzer (-fanalyzer).
It can now draw beautiful Unicode diagrams showing exactly how you went out-of-bounds.
See https://inbox.sourceware.org/gcc-patches/[email protected]/ too.
Thank you to the wonderful David Malcolm for implementing this - who also does a tonne of work with mentoring for GCC's GSoC programme, and working on docs to help new people get into GCC: https://gcc-newbies-guide.readthedocs.io/en/latest/index.html.