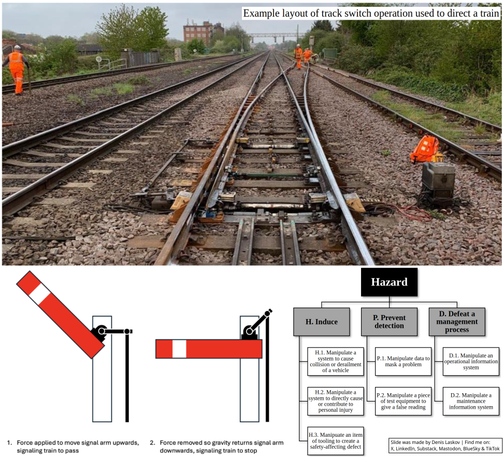
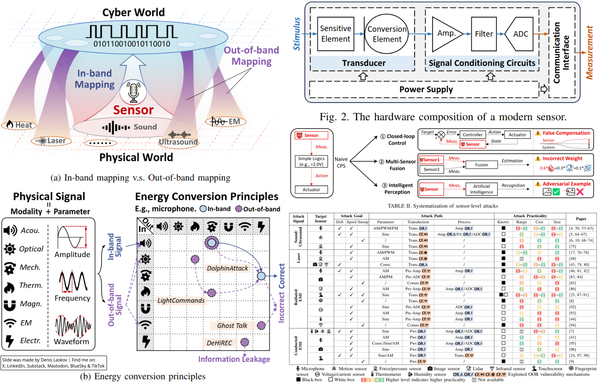
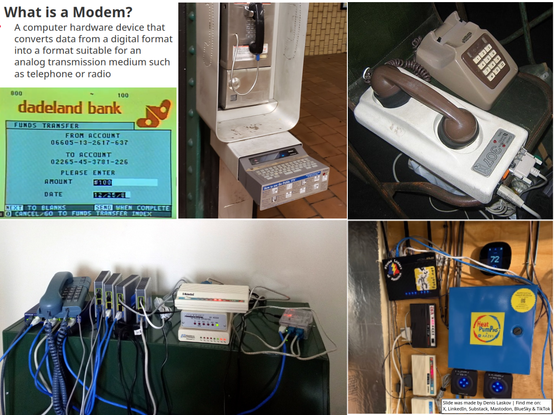
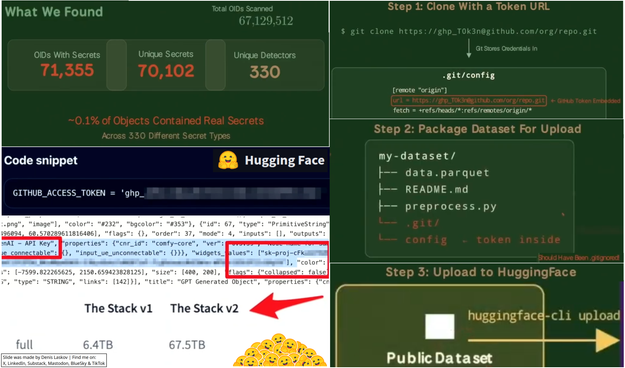
Hacking railroads to cause real damage: cyberattacks with impacts on safety and physical security. 🚂🚃🚃၊၊||၊👨🏻💻🩸
More details on:
LinkedIn: https://www.linkedin.com/posts/dlaskov_railroad-cybersecurity-rail-share-7467277595546378240-jz7r/
Substack: https://it4sec.substack.com/p/hacking-railroads-to-cause-real-damage