New IPs & some attribution clues related to the TA exploiting #CVE_2022_42475:
139.99.35[.116
139.99.37[.119
194.62.42[.105
45.86.231[.71
45.86.229[.220
185.250.149[.32
137.175.30[.138
146.70.157[.133
155.138.220[.254
#JA3:
bf2b95ac267823f6588b2436bc537b26
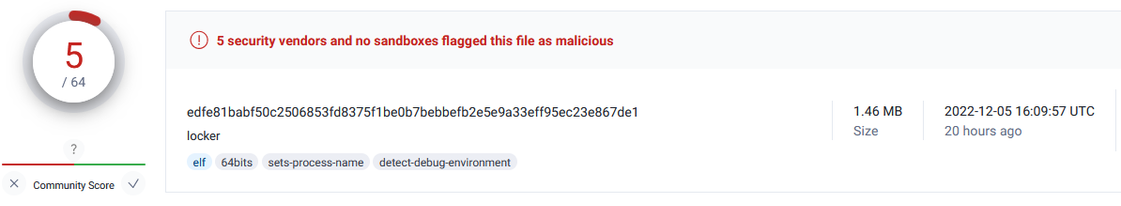
FG x64: https://virustotal.com/gui/file/0184e3d3dd8f4778d192d07e2caf44211141a570d45bb47a87894c68ebebeabb/details
Linux x64: https://virustotal.com/gui/file/23f2536aec6a4977a504312ff5863468ba2900fece735acd775d0ae455b4cd4d
Old Windows: https://www.virustotal.com/gui/file/61aae0e18c41ec4f610676680d26f6c6e1d4d5aa4e5092e40915fe806b679cd4
TA was less careful with the windows samples - left us some clues:
- GBK (Chinese) encoding of the computer info (later changed to utf-8)
- UTC+8 compile time string inside sample (exactly 8 hours ahead of PE compile time)