I shared this on LinkedIn because supposedly when you're unemployed, that's where you're supposed to "get noticed". Then I realized, infosec.exchange may also appreciate it.
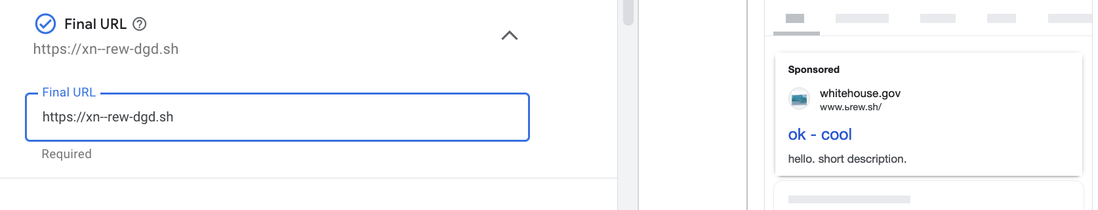
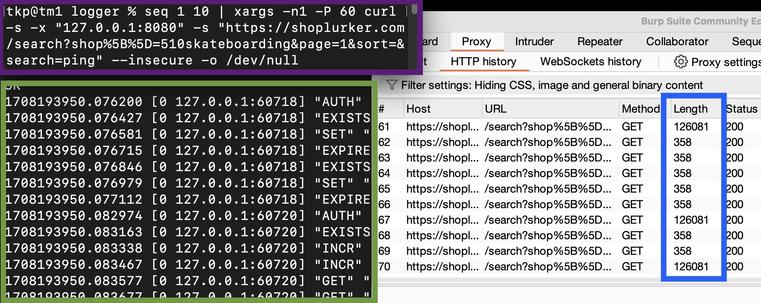
Saw a post about a potential Punycode attack on a popular MacOS package manager using Google ads. ( https://github.com/Homebrew/install/issues/866 ). Not sure how the attackers are pulling that one off. The 2nd image in this post shows that Google search is outputting punycode properly (at least for the character I used).
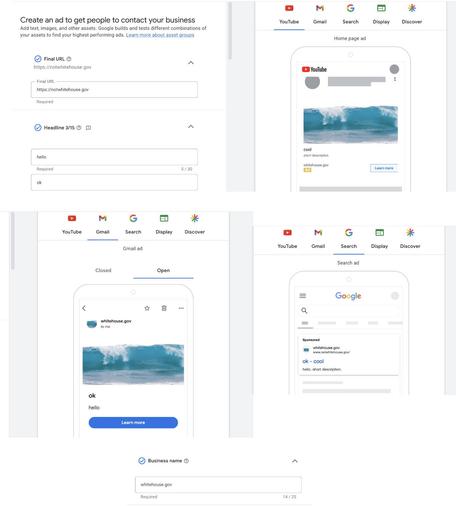
While taking a look at the ad buying process I decided to see if I could recreate all of the reports I've seen for years about spoofing urls in ads. Turns out the trust of the business name is the issue. Since it's election season, why not use Whitehouse.gov as an example?
Google search displays the final destination link in the results, which makes the url of that ad more clear, the others, not so much.
I should note I didn't complete the buying process by paying for the ads, so I can't fully confirm these ads getting pushed into the wild and seen by others. These are just previews of the how the ads are supposed to look according to Google.