| Homepage | https://hasherezade.net |
| https://twitter.com/hasherezade |
@hasherezade
- 1.4K Followers
- 34 Following
- 42 Posts
Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer.
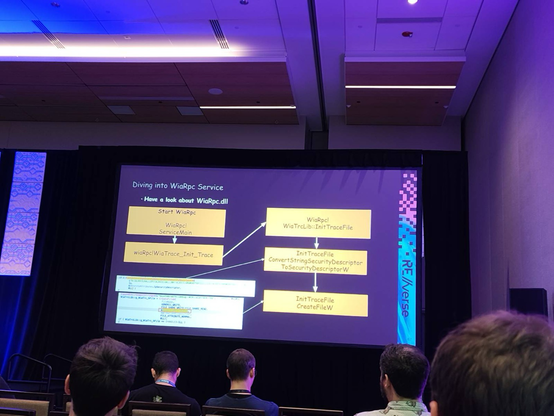
I just got back home from @REverseConf . I had an amazing time, and I want to thank the organisers and all the people I met! The talks went great, and I was honoured to be part of the process of choosing and refining them. If you are thinking about where to submit next year, I highly recommend this event, in beautiful Orlando!
Now you can use #HollowsHunter it in the classic mode, as well as in ETW mode - as a multi-threaded listener.
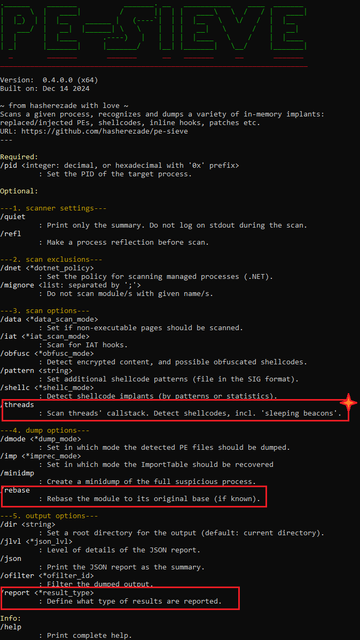
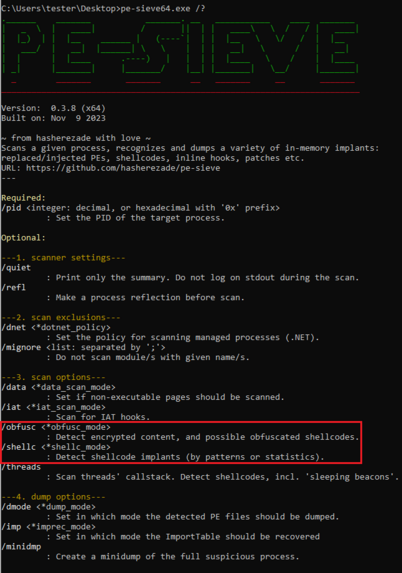
New #PEsieve
& #HollowsHunter (v0.4.0) are released: https://github.com/hasherezade/pe-sieve/releases & https://github.com/hasherezade/hollows_hunter/releases - A lot has changed in the new version, check it out!
& #HollowsHunter (v0.4.0) are released: https://github.com/hasherezade/pe-sieve/releases & https://github.com/hasherezade/hollows_hunter/releases - A lot has changed in the new version, check it out!
In my new blog for #CheckPointResearch I propose a new injection technique, using the Thread Name API - check it out! 💙 : https://research.checkpoint.com/2024/thread-name-calling-using-thread-name-for-offense // #ThreadNameCalling #processInjection
Thread Name-Calling - using Thread Name for offense - Check Point Research
Research by: hasherezade Highlights: Introduction Process injection is one of the important techniques used by attackers. We can find its variants implemented in almost every malware. It serves purposes such as: Due to the fact that interference in the memory of a process by malicious modules can cause a lot of damage, all sorts of AV […]
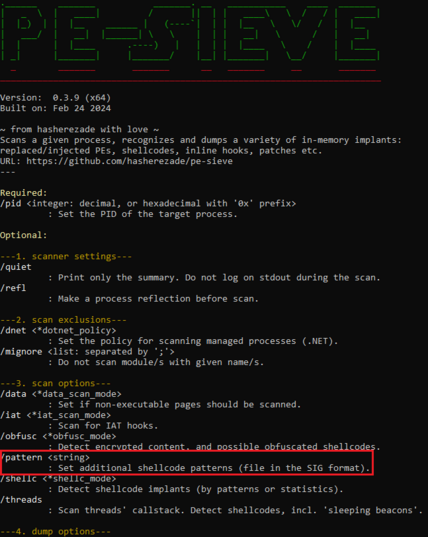
New #PEsieve/#HollowsHunter (v0.3.9): https://github.com/hasherezade/pe-sieve/releases/ & https://github.com/hasherezade/hollows_hunter/releases - now you can search for your own signatures in memory. Details: https://github.com/hasherezade/pe-sieve/wiki/4.11.-Detect-shellcode-by-custom-patterns-(pattern). Check it out!
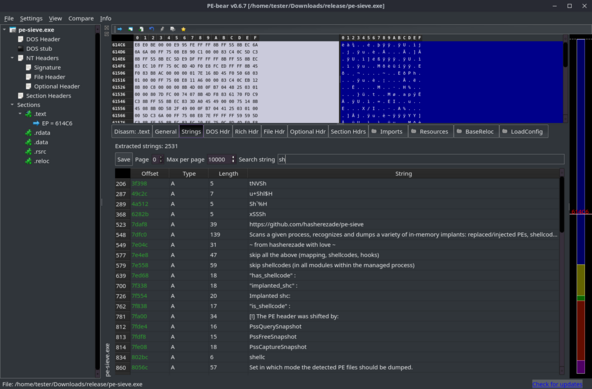
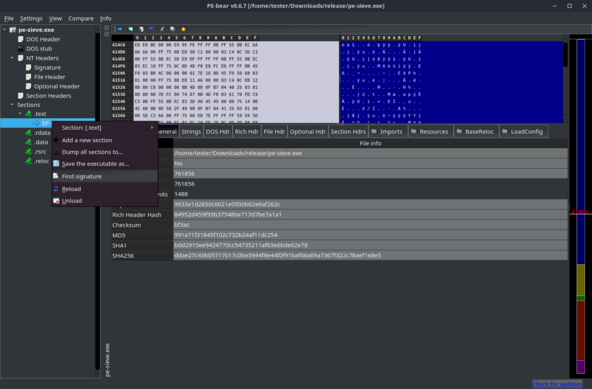
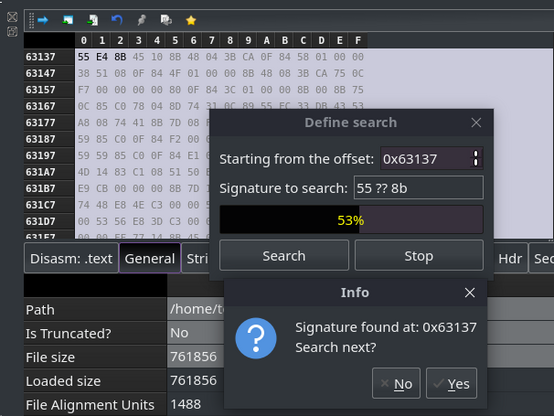
New Year with new #PEbear - release 0.6.7 is ready! I added some new features, such as Strings view, searching for binary patterns, remapping of PEs dumped from memory, and more. Check it out: https://github.com/hasherezade/pe-bear/releases/
New #PEsieve/#HollowsHunter (v0.3.8) is out: https://github.com/hasherezade/pe-sieve/releases & https://github.com/hasherezade/hollows_hunter/releases
- including features discussed in the following video: https://www.youtube.com/watch?v=liSSm1sWBGg
- including features discussed in the following video: https://www.youtube.com/watch?v=liSSm1sWBGg
I did a writeup on #Magniber - an obfuscated #ransomware using raw #syscalls to call functions. The writeup has more of a tutorial form, demonstrating usage of some of my tools (mainly #TinyTracer) in action, and also sharing some of my approaches & workflow. Check it out: https://hshrzd.wordpress.com/2023/03/30/magniber-ransomware-analysis/
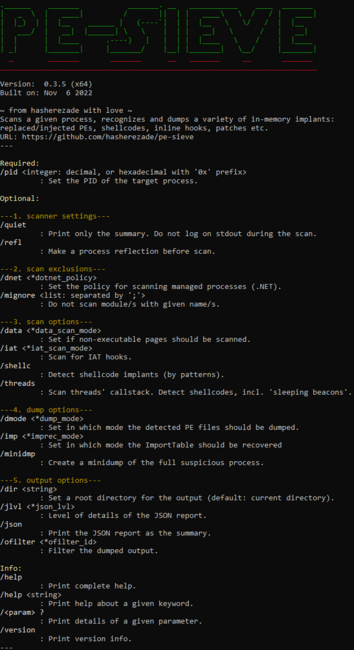
New #PEsieve/#HollowsHunter (v0.3.5): https://github.com/hasherezade/pe-sieve/releases/ & https://github.com/hasherezade/hollows_hunter/releases - with some bugfixes & improvements. Check it out!