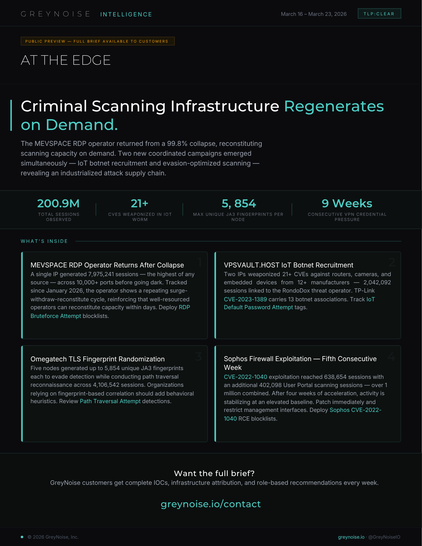
200,886,675 sessions. 101 unique source IPs. March 16–23, 2026.
GreyNoise At The Edge intelligence brief highlights:
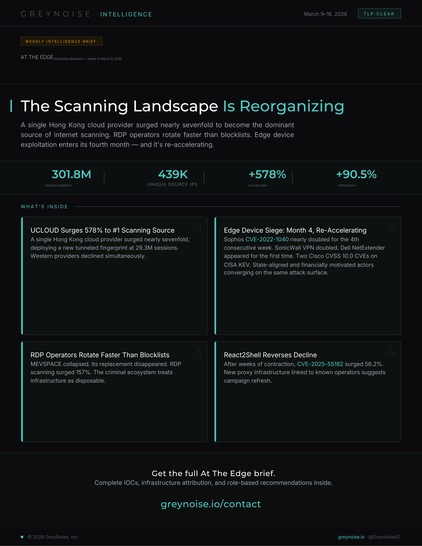
1. The MEVSPACE RDP brute-force operator returned after a 99.8% infrastructure collapse — single IP generated 7,975,241 sessions before deliberately withdrawing after 4 days. GreyNoise has tracked a surge-withdraw-reconstitute cycle since January 2026, reinforcing that well-resourced operators can reconstitute capacity within days.
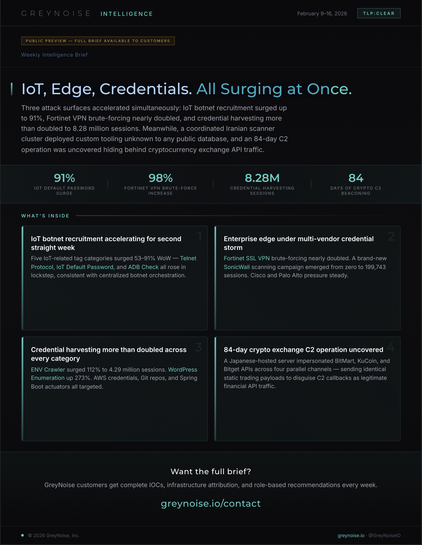
2. Two coordinated campaigns emerged: VPSVAULT.HOST (IoT worm weaponizing 21+ CVEs against 12+ manufacturers) and Omegatech (TLS fingerprint randomization with 5,854 unique JA3s per node).
3. Sophos CVE-2022-1040 exploitation stabilized at 638,654 sessions in its fifth consecutive week. Enterprise VPN credential pressure reached week 9 across five vendors with 2.9M+ combined sessions.
4. n8n CVE-2026-21858 (CVSS 10.0) reached 118,086 sessions with links to MuddyWater and ZeroBot. ICS/SCADA reconnaissance expanded with new HMI and PLC vulnerabilities trending.
🔗 https://www.greynoise.io/resources/at-the-edge-clear-032326
#ThreatIntel #CyberSecurity #InfoSec #GreyNoise