New: Anime streaming service Crunchyroll has confirmed a data breach involving customer service ticket information following an incident with a third-party vendor.
Alexandre Dufresne
- 20 Followers
- 108 Following
- 332 Posts
February was anything but quiet at GreyNoise, from our 2026 State of the Edge Report to new edge attack research, Ivanti + BeyondTrust deep dives, and a packed March of events, check it all out in this month's Noiseletter! 🚀
https://www.greynoise.io/resources/noiseletter-february-2026
Whoops. The data broker giant LexisNexis has suffered another data breach. LN says the data taken was no big deal. The group claiming credit for the breach claims otherwise, of course.
This brings back memories of previous breach stories. One of my first big scoops that made the WaPo dead tree edition's front page involved a breach at LexisNexis in 2005 that exposed >300k consumer records. That breach was from a group of 15-18y/os in the US who also social engineered T-Mobile into giving them access to Paris Hilton's cell phone and the nudes w/in.
In 2013, I published a scoop about a LexisNexis breach that came from group of criminal hackers who had seized control over ssndob[.]ru, then the largest ID theft service in the underground. In that months-long investigation, we found the hackers had installed backdoors on servers at LexisNexis, Dun & Bradstreet, and Kroll and were using them as part of a small and custom data broker botnet.
https://krebsonsecurity.com/2013/09/data-broker-giants-hacked-by-id-theft-service/
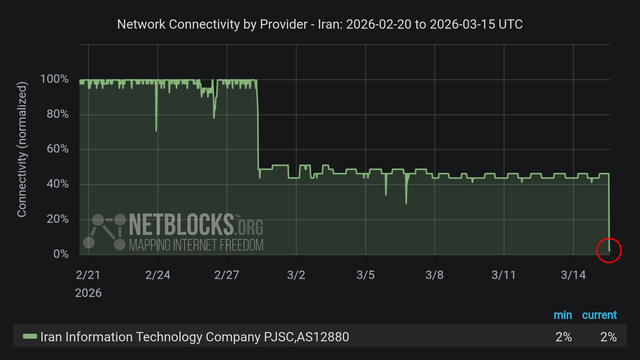
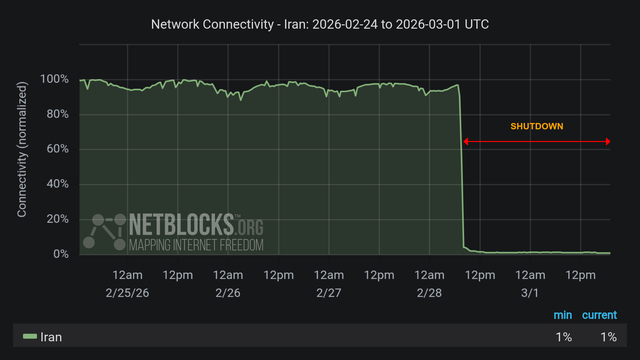
⚠️ Update: #Iran has now been cut off from the world for 36 hours with metrics showing connectivity at 1% of ordinary levels.
The internet blackout imposed on Saturday morning continues to limit Iranians' access to information as the war with the US and Israel widens regionally.
I usually find Louis Rossmann a bit intense, but his latest video was super enjoyable.
Humour is often the best way to bring complex issues to light while making people interested. The Norwegian Consumer Council really hit the ball, here. Watch their brilliant video on #enshittification:
- Louis Rossmann’s Take: Norwegian Government comes out swinging on enshittification
- The Original Video: A Day in the Life of an Ensh*ttificator

Norweigan Government comes out swinging on enshittification
It's like AWS security defaults all over again... 🤦♂️
Google Map API keys by default unrestricted, giving any visitor to your website with an embedded map also access to your other Google things, like the Gemini API! I can't image how confused I would've been had my bill ballooned due to visitors hammering Gemini with my, by design publicly exposed, Maps API key. 😬
https://trufflesecurity.com/blog/google-api-keys-werent-secrets-but-then-gemini-changed-the-rules
RCE in React Server Components, impacting React and Next.js. I usually don't say this, but patch right freakin' now. The React CVE listing (CVE-2025-55182) is a perfect 10.
https://www.wiz.io/blog/critical-vulnerability-in-react-cve-2025-55182
https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components
https://nextjs.org/blog/CVE-2025-66478