Phishing related to Post Finance (Swiss bank), pretty well done:
You receive an email like this one below. You check the sender and see it is coming from another domain (1st warning):
no-replay@lfm[.]ch
Notice also it is “no-replay” and it should be “no-reply" to simulate an automated mailbox. So we have now two warnings.
You check the footer of the email:
“Don't like these emails? Unsubscribe or Manage Email Subscriptions
Powered By FluentCRM”
Since when a CRM would send this type of email? There you have your third warning.
You notice the big gap between email content and footer (see image), and you find some gibberish text that is in white foreground and background. Check next image. And there you have your fourth warning.
Next: the link. It points to (this is a URLScan result, safe to click)
https://urlscan.io/result/d003eb47-1414-4842-83f6-cb7b69890bc5/
And you see it redirects you to:
https://oustrup-landbrug[.]dk/pf/
URLScan doesn't go to a second redirection, so if I check with a sandbox, you will see it takes you to:
https://salonfigaro[.]dk/ch/PF/Login.php
Which is perfect copy of Post Finance login page.
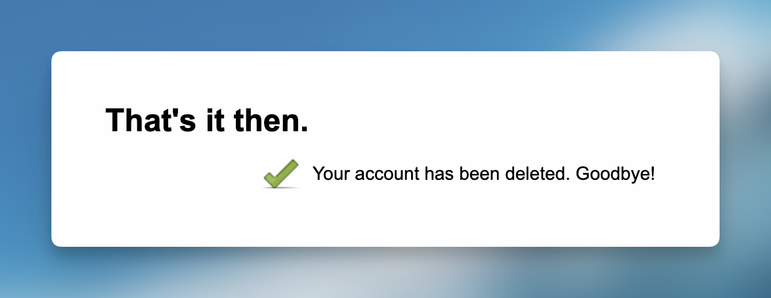
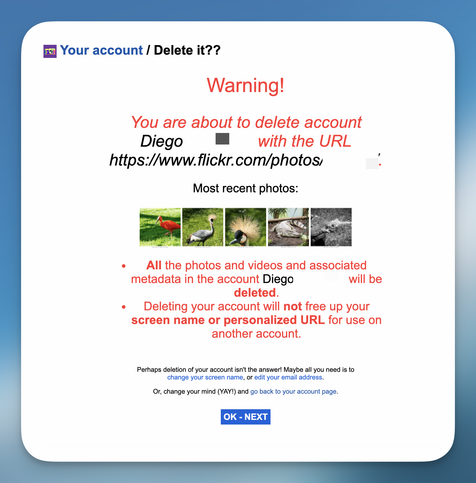
If you put fake data, it takes you to this page:
https://salonfigaro[.]dk/ch/PF/Account/Waiting.php and keeps showing last image. And, of course, you will never get passed it.
To summarise, plenty of warnings that can help you detect a phishing. What is really interesting is the fact that threat actors don't just send you a phishing email hoping it does not get filtered, they really work hard to:
- detect an email domain not having SPF properly configured
- use a CRM to send emails
- hack their way into two web servers
- redirect 2 times to defeat link analysis services
So, nicely tried, and no luck with me. But I wonder how many people might have fallen for it...