| Beacons | https://beacons.ai/dacbarbos |
| Keybase | https://keybase.io/dacbarbos |
DACBARBOS Brand
- 140 Followers
- 1,090 Following
- 2.6K Posts
Torvalds takes a stand on social media shaming with kernel development.
MT @[email protected]
💡 CSS Tip!
Get the screen width and height using a few lines of CSS.
✅ Powered by @property (Now available in all the browsers)
✅ Unitless values so you can easily use them inside any formula
✅ Updates on screen resize (No need for JS)
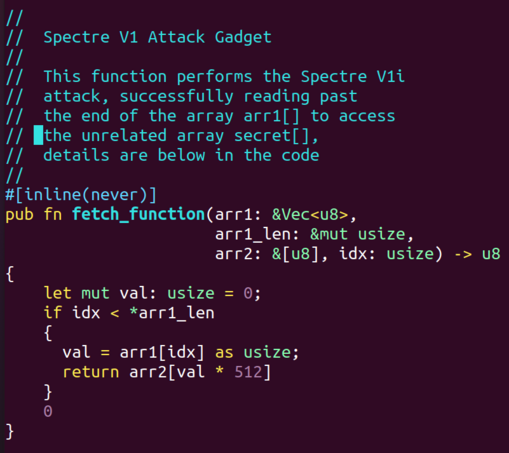
In Rust We Trust?!?! We now have a working Spectre V1 attack for Rust. Using our Spectre V1 transient execution attack, we are able to force a bounds-checked Rust array to perform an arbitrary buffer overread. I've attached the function that we are attacking with Spectre V1. https://twitter.com/ToddMAustin/status/1730623011903168724
Todd Austin (@ToddMAustin) on X
In Rust We Trust?!?! We now have a working Spectre V1 attack for Rust. Using our Spectre V1 transient execution attack, we are able to force a bounds-checked Rust array to perform an arbitrary buffer overread. I've attached the function that we are attacking with Spectre V1.
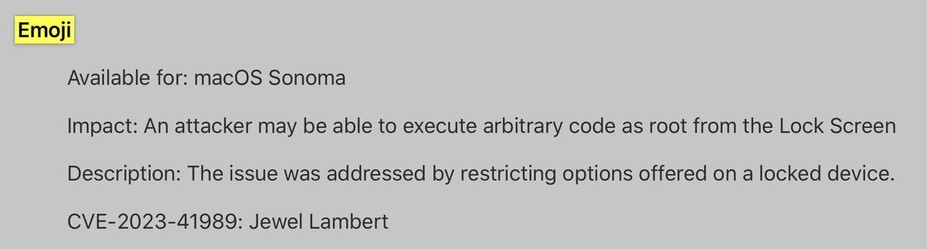
A lot neat 🍎-bugs patched in macOS 14.1: https://support.apple.com/en-us/HT213984
...but especially intrigued by CVE-2023-41989 (credit: Jewel Lambert):
"An attacker may be able to execute arbitrary code as root from the Lock Screen" ...via Emoji!? Ha 🤔😈 (via @[email protected]) #infosec