| Pronouns | he/him |
| Location | NoVA |
Compuguy, Friend of Kittehs
- 150 Followers
- 610 Following
- 283 Posts
This is "the calm corner" a waiting room for those who need a safe and calm enviroment. This is an autistic waiting room 💖💖💖💖💖💖
It is cosy and quiet here, all I ever need in a train station.
Via Katie Phang:
READ THIS.
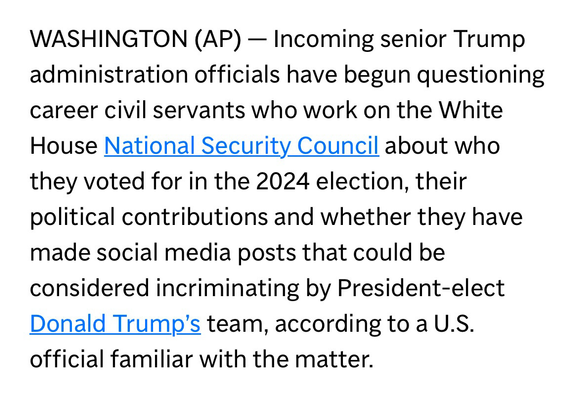
THEN READ IT AGAIN.
WASHINGTON (AP) - Incoming senior #Trump administration officials have begun questioning career civil servants who work on the White House National Security Council about who they voted for in the 2024 election, their political contributions and whether they have made social media posts that could be considered incriminating by President-elect Donald Trump's team, according to a U.S. official familiar with the matter.
@iagox86 @dangoodin @GossiTheDog @h0wdy Can’t speak for CISA but it’s very popular in Europe, mostly universities and government entities. Volexity and Google TAG also witnessed several 0-day campaigns.
But definitely not worth the dramatic coverage we’re seeing, looks like the CUPS debacle was not enough.
@dangoodin @swapgs @GossiTheDog @h0wdy Oh yeah, the big vuln last year, that CISA told us was under active exploit, was in memcached and was a pain to exploit.
I wanted to work on Zimbra more, their security seemed questionable, but we decided that they weren't popular enough.
That being said, CISA seemed oddly interested in Zimbra stuff.
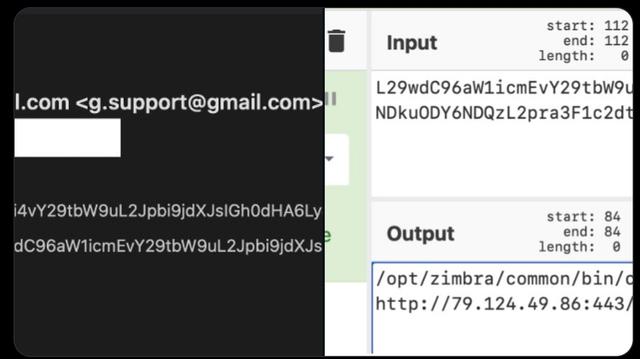
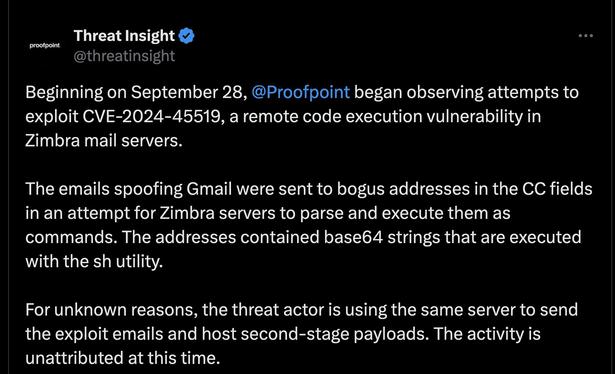
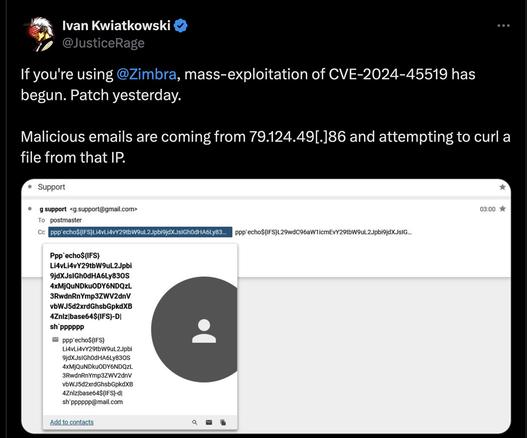
If you're using @zimbra, mass-exploitation of CVE-2024-45519 has begun. Patch yesterday.
Malicious emails are coming from 79.124.49[.]86 and attempting to curl a file from that IP.
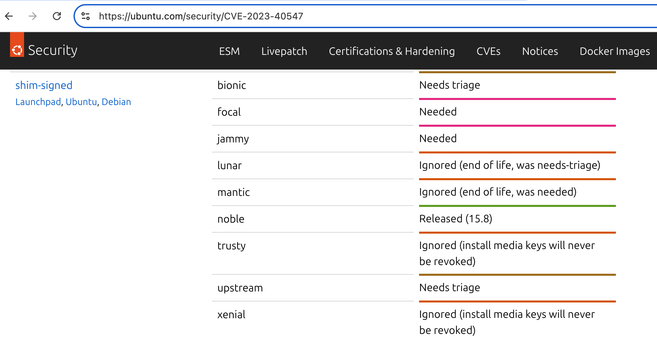
Indeed. Ubuntu is asleep at the wheel.
"Needs triage" / "Needed" for a CVE that is 7 months old leaves something to be desired.
https://ubuntu.com/security/CVE-2023-40547
If anybody has been playing along with the "what SBAT does my system have?" game, take caution:
In a true heisenbug sense, note that the Linux ISO you boot with may *itself* update the SBAT of the system you are inspecting.
For example, the process of booting a Mint 22 ISO on a Windows system to check the SBAT level will in and of itself update the SBAT to the level that protects against CVE-2022-2601. As such, I previously (incorrectly) concluded that a July 2024 Windows 11 system already has a mitigation for CVE-2022-2601. This is not correct. I fell victim of using a tool for measuring something that actually changes the thing I'm measuring before I got the chance to make the measurement. 🤦♂️
Booting such a system with an Ubuntu 22.04 Server ISO will show that July 2024 Windows 11 does *not* have a CVE-2022-2601 mitigation.
The August SBAT update that Microsoft pushed out for CVE-2022-2601 does indeed block CVE-2022-2601 exploitation. And it appears to be the first time that Microsoft has deployed an SBAT update to Windows systems. However, it also has mitigations for half a dozen *newer* CVEs.
Microsoft does indeed have an update page for CVE-2023-40547 (RCE in HTTP boot support):
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-40547
But they didn't bother with CVE-2023-40546, CVE-2023-40548, CVE-2023-40549, CVE-2023-40550, or CVE-2023-40550.
The fact that Ubuntu (and friends) wasn't prepared for mitigations being deployed for a set of 7-month-old vulnerabilities is, well, disappointing. Folks living in the SecureBoot world are going to have to be prepared for such an update happening, and one very well may happen like this again in the future. Hopefully distros will take SecureBoot-related updates more seriously in the future.