The Calyx Institute
@calyxinstitute
- 3.7K Followers
- 164 Following
- 648 Posts
Our mission is to educate the public about privacy in digital communications and to develop tools that anyone can use. By embracing "privacy by design," we help make digital security and privacy more accessible to everyone. Help support our nonprofit mission-- become a member and get a hotspot with unlimited wifi or a phone with CalyxOS! https://members.calyxinstitute.org/enroll/membership
Our staff were looking forward to participating in RightsCon in Zambia this year, and we are disappointed to hear that all of the organizers' hard work has been dashed by the sudden cancellation of the conference. The Calyx Institute stands in solidarity with the teams at RightsCon and Access Now, and we look forward to reconvening with our digital rights community at RightsCon in the future. https://www.rightscon.org/rc26-statement/
Despite a “lack of proper detailed security documentation” for Microsoft’s Government Community Cloud High, a suite of cloud-based services intended to safeguard the nation’s most sensitive information, and reviewers' “lack of confidence in assessing the system’s overall security posture,” the Federal Risk and Authorization Management Program, or FedRAMP, authorized the product anyway, bestowing what amounts to the federal government’s cybersecurity seal of approval. https://www.propublica.org/article/microsoft-cloud-fedramp-cybersecurity-government

Federal Cyber Experts Thought Microsoft’s Cloud Was “a Pile of Shit.” They Approved It Anyway.
A federal program created to protect the government against cyber threats authorized a sprawling Microsoft cloud product, despite the company’s inability to fully explain how it protects sensitive data.
FSFE talk about the Cyber Resilience Act on their podcast: https://fsfe.org/news/podcast/2026/episode-48.en.html Free Software developers this is the episode for you to find out what options you have and what lies ahead.
Next month, SCOTUS will hear oral arguments in Chatrie v. United States on the government’s use of geofencing warrants to obtain a person’s cell phone data. Their ruling could have major implications for how and when law enforcement and the state can access Americans’ sensitive personal information in the digital age. https://newrepublic.com/article/207706/geofencing-supreme-court-fourth-amendment-test-chatrie
A Tennessee grandmother spent nearly six months behind bars after artificial intelligence facial recognition software wrongly identified her as a suspect in a bank fraud case – in North Dakota – a state she says she had never even visited. https://www.the-independent.com/news/world/americas/crime/tennessee-grandmother-ai-arrest-error-north-dakota-b2938261.html
TODAY: Join CryptoHarlem at 6pm EST for an in-depth conversation on cybersecurity with Gabrielle B, a multi-award-winning cybersecurity expert and former cyber defense specialist. Watch online:
https://talkstudio.streamlabs.com/Mgvhwl4m3IbJ More about CryotoHarlem: https://cryptoharlem.com
https://talkstudio.streamlabs.com/Mgvhwl4m3IbJ More about CryotoHarlem: https://cryptoharlem.com
Lookout Threat Labs has discovered DarkSword, a full iOS exploit chain and payload for iPhones running iOS versions between iOS 18.4 and 18.6.2. This threat was deployed by the same unknown, likely Russian, threat actor who also deployed the Coruna exploit chain reported earlier this year. https://www.lookout.com/threat-intelligence/article/darksword
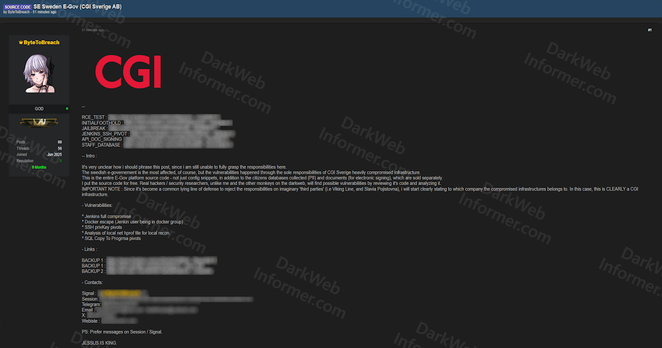
A threat actor has leaked the entire source code of Sweden's E-Government platform, claiming it was obtained through a heavily compromised CGI Sverige AB infrastructure. CGI Sverige is the Swedish subsidiary of global IT services giant CGI Group and manages critical government digital services.The source code is being released for free with multiple backup download links, while citizen databases are sold separately.
https://darkwebinformer.com/full-source-code-of-swedens-e-government-platform-leaked-from-compromised-cgi-sverige-infrastructure/
https://darkwebinformer.com/full-source-code-of-swedens-e-government-platform-leaked-from-compromised-cgi-sverige-infrastructure/
How to film federal agents in the field — advice for independent journalists https://freedom.press/digisec/blog/how-to-film-federal-agents-in-the-field-advice-for-independent-journalists/
Clients of a long-running email marketing platform are getting targeted with a phishing campaign telling them that their emails would begin inserting a “‘Support ICE’ donation button” into every email they send. Scammers are trying to capitalize on people’s revulsion to ICE by coming up with strategies that would trick users into trying to log into their accounts to disable the setting. In reality, clients are revealing their username and password to hackers. https://www.404media.co/ice-phishing-scammers-are-sending-support-ice-emails-to-steal-credentials/