| https://twitter.com/bugch3ck | |
| Github | https://github.com/bugch3ck |
| BlueSky | https://bsky.app/profile/bugch3ck.bsky.social |
Jonas Vestberg
- 336 Followers
- 233 Following
- 146 Posts
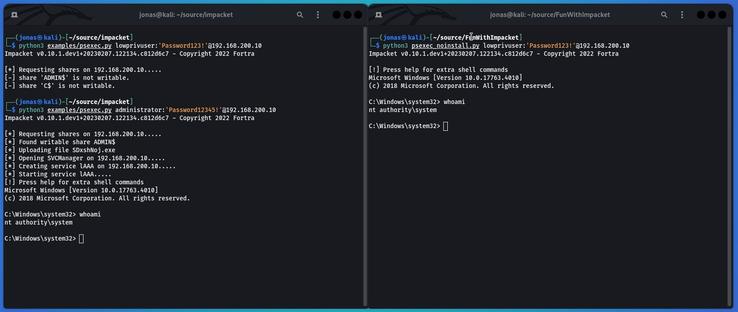
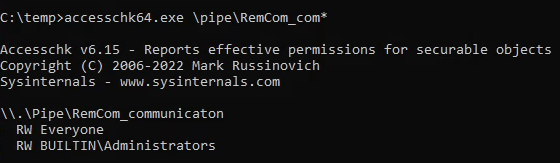
The vulnerable code is in RemComSvc, setting an empty DACL on the pipe.
https://github.com/kavika13/RemCom/blob/master/RemComSvc/RemComSvc.cpp#L77
Kinda excited.. the official program for Disobey 2023 is out!

I wanted to take a few moments and apologize to many of my former students.
In the past I said the industry needs people who look at security as a vocation and an avocation.
I was wrong.
Have a life outside of this industry.
Have hobbies that have nothing to do with your computer.
Get outside.
The problems of the industry are not problems of people not working hard enough.
They are not problems of people not being "hard core" enough.
They are problems of education and resource prioritization.
I was wrong.
I am sorry.
Stop breaking yourself on rocks for people who don't really care if you break yourself on rocks.
A not-so-common NTLM reflection attack allowing for arbitrary read/write. Basically EoP from user to SYSTEM.
Tracked as #CVE-2023-21746 - Windows NTLM EoP
Soon more details --> http://localpotato.com
cc
@splinter_code