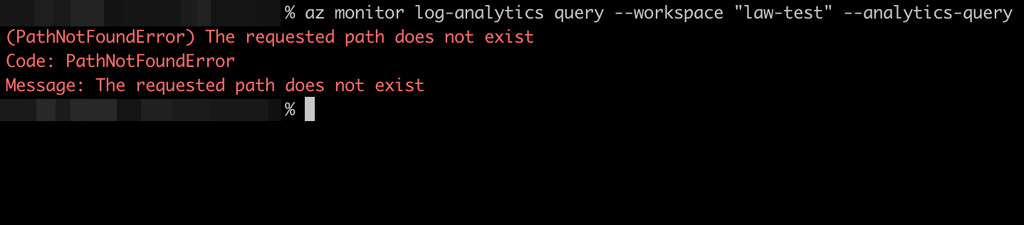
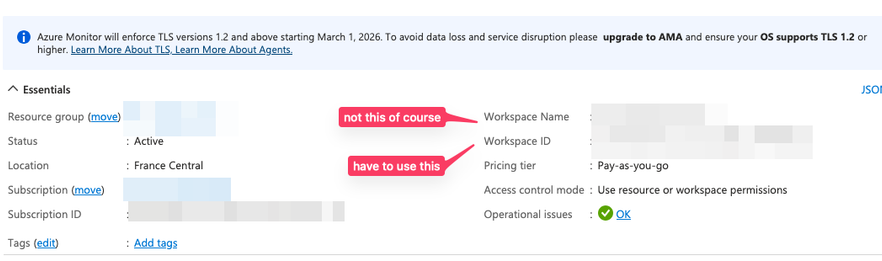
Day 544. When querying #Azure Log Analytics logs over the Azure CLI, if you use the workspace name the CLI will tell you "PathNotFound" which is not really helpful. You need to use the workspace ID instead of the workspace name, which of course is a totally different thing.
Daily dosis of shit experienced on Microsoft Azure.
This account is obviously not affiliated with Microsoft.
| Short | https://azsh.it |
| Short Example | https://azsh.it/45 |