| Webside | https://asante.dev |
asante
- 53 Followers
- 112 Following
- 548 Posts
So, I recently saw some quiet discussion about a paper where researchers reverse-engineered and disclosed some attacks against PhotoDNA, the very-super-duper-secret algorithm used by tech megacorps to scan for illegal images.
They didn't make any code public, and so... I did: https://github.com/ArcaneNibble/open-alleged-photodna
A _complete_ reverse-engineering and commented Python reimplementation of the algorithm from publicly-leaked binaries.
This means that studying the algorithm and any potential flaws is now much more accessible.
This took only about two days (once I knew that there even _was_ a leaked binary to compare against), which just goes to again show that security through obscurity never works.
🔁 encouraged
https://events.ccc.de/2026/03/15/gpn24/

24. Gulaschprogrammiernacht
gpn24.de – Gulasch at the Scale of Chaos Der Entropia e.V. lädt euch herzlich zur 24. Gulaschprogrammiernacht mit dem Motto „Gulasch at the Scale of Chaos“ ein! 4.–7.6.2026 HfG und ZKM, Lorenzstraße 15, 76135 Karlsruhe TL;DR: Die GPN ist eine offene, spendenfinanzierte Community-Veranstaltung, bei der du zum Beispiel gemeinsam hacken, Gulasch essen oder Vorträge schauen kannst. Wie bereits zur letzten GPN ist eine Anmeldung notwendig. 80.000 € – Hilf mit, dieses Spendenziel zu erreichen. Die GPN wird vor allem durch euch und eure Spenden ermöglicht. Wir brauchen jede (auch deine!) Spende, um auch in Zukunft eine Gulaschprogrammiernacht zu feiern! Die GPN hat sich die letzten Jahre entgegen unserer Erwartungen finanziell nicht getragen.
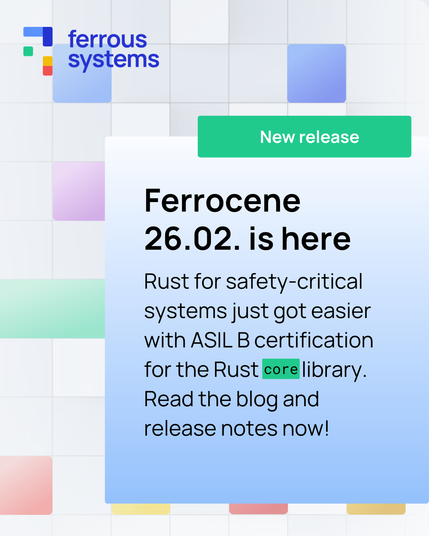
Ferrocene 26.02.0 is out 🦀
Highlights:
👉 ISO 26262 ASIL B certification for part of Rust core
👉 Qualified Rust toolchain for safety-critical systems
If you’re at #ew26, come by booth 4-402 to talk to us about #embeddedRust (and get some stickers).
Read more: 🔗 https://ferrous-systems.com/blog/ferrocene-26-02-0/
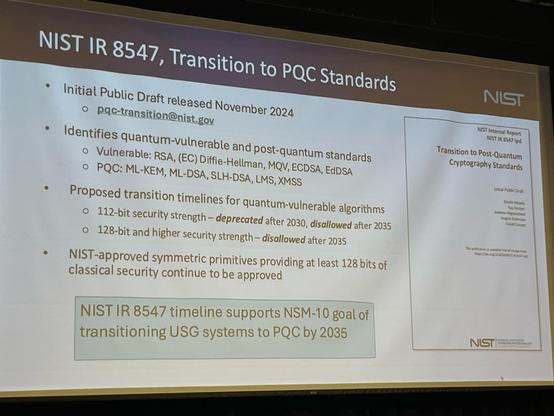
@wolf480pl @filippo there's a nice slide deck by Samuel Jaques from CHES 2024 giving insights on Grover's algorithm for this case:
https://ches.iacr.org/2024/Jaques_CHES_2024.pdf
From my understanding, the big-o sqrt speed up basically hides big constants that result in practical limitations, which results in an effort of 2^64 being not achievable.
Dustin Moody from NIST: “you don’t need more than 128 bits of symmetric keys for post-quantum security” #rwc2026
Say it louder, for the people in the back!
Happy to announce I won the European Open Source Academy Special Recognition for Skills and Education! @europeanOSacademy