Juanma Fernandez
- 356 Followers
- 89 Following
- 353 Posts
The Internet is falling down, falling down, falling down
Welcome back to another disaster - this time, an Auth Bypass in cPanel/WHM, tracked as CVE-2026-41940
Enjoy with us..
https://labs.watchtowr.com/the-internet-is-falling-down-falling-down-falling-down-cpanel-whm-authentication-bypass-cve-2026-41940/

The Internet Is Falling Down, Falling Down, Falling Down (cPanel & WHM Authentication Bypass CVE-2026-41940)
Hello! Yes, it's all a disaster again! Let's get this party started: 0:00 /0:12 1× No comments today, so imagine this: * We wrote something that we find very funny, * Nobody else gets it, * But everyone humors us It's your typical watchTowr Labs blog introduction. What Is cPanel & WHM?
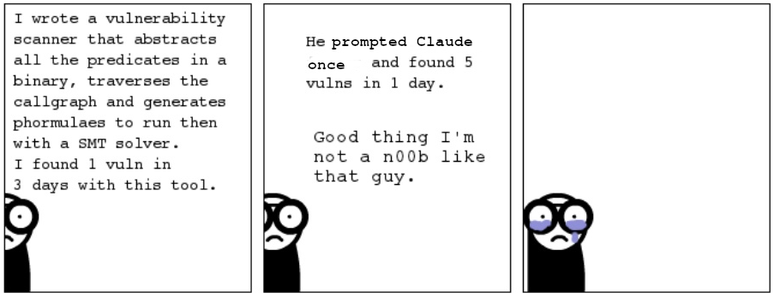
Who would have imagined that "raising the bar" in security was flooding internet with the vomit of AI so people can not read real articles or proof of concepts about public vulnerabilities.
If someone wrote something about the details of a vuln, you will not find it using search engines because now it has been buried by the infectious pus of bots spamming shit.
RegPwn was a Windows 0-day that we were using for LPE in our Red Team for a year (discovered by Filip D. In January 2025). Unfortunately it got fixed 🥲
Good bye RegPwn 🫡
https://www.mdsec.co.uk/2026/02/total-recall-retracing-your-steps-back-to-nt-authoritysystem/