| https://www.linkedin.com/in/wysopal | |
| https://www.twitter.com/WeldPond :verified: | |
| Wikipedia | https://en.m.wikipedia.org/wiki/Weld_Pond |
Chris Wysopal
- 4.8K Followers
- 238 Following
- 478 Posts
I just learned the sad news that Peter Neumann has passed away.
Peter Neumann shaped how a generation of security people learned to think about risk. As editor of RISKS Digest, he gave many of us coming up in the 1990s and early 2000s a steady education in the real-world consequences of computer failures. His work made the field more serious, more thoughtful, and more honest. He will be missed.
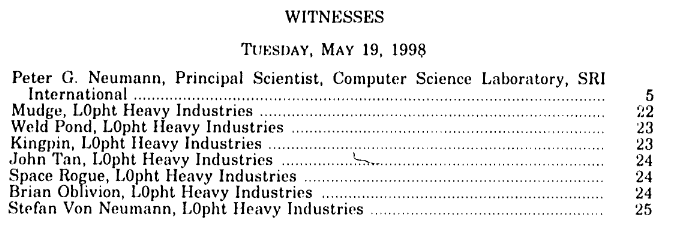
I first met Peter when we both testified at the 1998 Senate Governmental Affairs Committee meeting on Government Security where the L0pht testified. The combination of Peter and the L0pht made the hearing more powerful even if us hackers stole the spotlight.
Neumann and the L0pht made the same argument from two different directions. Neumann gave the institutional, systems-engineering view: the country was becoming dependent on brittle, interconnected systems that were never designed for security, reliability, or survivability. The L0pht gave the field evidence: here are the actual flaws, here is how attackers think, here is how cheaply and quickly these systems can fail in practice.
Neumann supplied the credibility of a long-time researcher warning that this was not just “hackers breaking into things,” but a structural failure of technology markets, procurement, engineering discipline, and risk management. The L0pht supplied the proof that the warnings were not theoretical. Together, we made the hearing unusually powerful: the academic risk community and the hacker community were telling the Senate the same thing, in different languages, before the rest of the world had fully caught up.
RE: https://infosec.exchange/@Weld/116100770024505311
🕯️ Jason Snitker "Parmaster" Memorial 🕯️
Feb 28, 2026 04:00 PM
Debra Kavaler Wysopal will be hosting this online memorial service for Parmaster along with Jason's family from Atlantic City, NJ.
Confirmed Speakers:
Par's Aunt
Deb
Mudge
John Lee
Tom Sloan (former Secret Service)
The memorial service will be recorded.
Registration Link: https://us02web.zoom.us/meeting/register/hYD6OW0URGaIUG5qA18zXw
My wife Deb and I are heartbroken to share the sad news that our old friend Jason Snitker AKA Parmaster has passed away.
Par was one of the sharpest and most elusive minds of the early underground hacking scene. As chronicled in “Underground”, he spent years navigating the emerging digital frontier, connecting with hackers internationally and repeatedly staying ahead of the United States Secret Service during a prolonged investigation in the early 1990s.
His story in “Underground” includes the Citibank investigation that helped trigger the pursuit, as well as his time in custody at Rikers Island, where he found himself playing Dungeons & Dragons.
Par’s life reflected both the intensity of the early hacking world and the very real consequences that came with it. He was part of a generation that explored the edges of a new technological landscape before most of the world even understood it existed.
There will be an online memorial gathering on Feb 28. More details to follow.
The old-school hacking community has lost a true original. Rest in peace, Par. If anyone has stories or memories, please share them here.
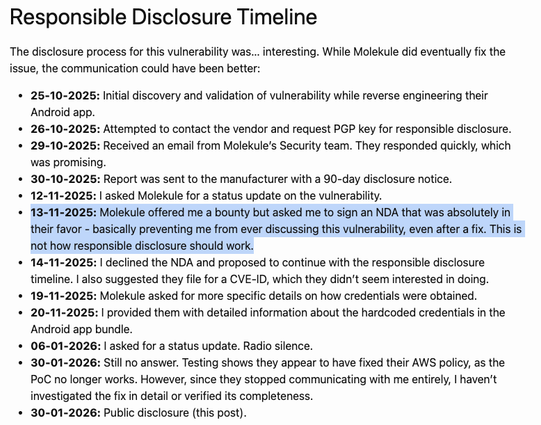
In order to collect a bug bounty, a researcher was required to sign an NDA to not discuss the vulnerability.