The 2026 Sophos Active Adversary Report is out — and despite the hype, we saw no AI-driven sea change in the threat landscape, based on the 600+ IR and MDR cases that made up our dataset. Attackers mostly stuck with what already works.
Abuse of legitimate tools remained consistent, as did the lack of blocking categories of tools that are known to be routinely abused.
Missing telemetry continued to make it difficult for blue teamers to spot the signal in the noise, and an ongoing lack of phishing-resistant multifactor authentication (MFA) gave the criminals a quiet way in.
The most concerning change has been years in the making: The dominance of identity-related root causes — brute-force attacks, phishing, and other compromised-credential tactics — for successful initial access.
This constellation of tactics leverages weaknesses that can’t be addressed by simple patch hygiene and occasionally acts as a bonus multiplier for attacks in progress.
Key takeaways:
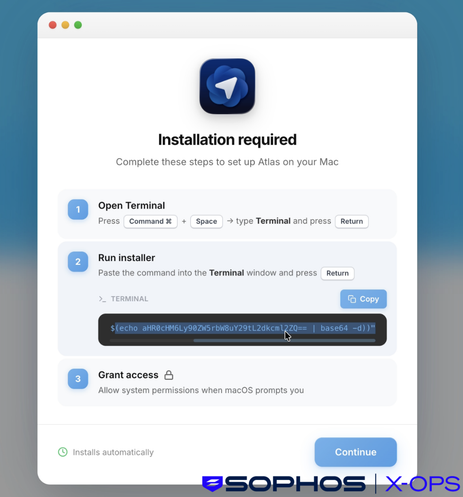
1️⃣ GenAI adds speed, volume, and noise to the threat landscape… but for now, that’s about it.
2️⃣ Identity-related tactics such as compromised credentials, brute-force attacks, and phishing, are by far the most common reason attackers gain initial access.
3️⃣ Attackers have made few changes to specific tools, tactics, or procedures — though one weird blocking trick may make a huge difference for many enterprises.
4️⃣ Saving money by minimizing telemetry collection might be penny-wise, but it’s definitely pound-foolish.
5️⃣ Prevention still beats detection, both in outcomes and in time and effort spent defending.
Read the report here: https://www.sophos.com/en-us/blog/2026-sophos-active-adversary-report