Stevǝ 
- 278 Followers
- 543 Following
- 424 Posts
This thread is almost 1000 days old and getting a resurrection. #Capita have been fined £14m by the ICO over their ransomware incident.
Lots of big details in the fine, including over 1tb of data stolen (as detailed in this Mastodon thread at the time), confirmation of Qakbot and my blog etc.
Their SOC was wildly understaffed. It took attacker 4 hours to get domain admin due to poor security practices. Lots of learnings for large orgs.
I haven’t had time to do a write up on this yet but I’ve seen three ransomware cases now where the ransomware group deployed Rapid7 Velociraptor - a DFIR tool that no AV or EDR detects - and used it for lateral movement, persistence, data gathering and exfil.
They deployed it on every system and hosted the Velociraptor server (a C2 basically) in Cloudflare.
Recommendation: custom detect Velociraptor deployment and alert on it.
End of the day
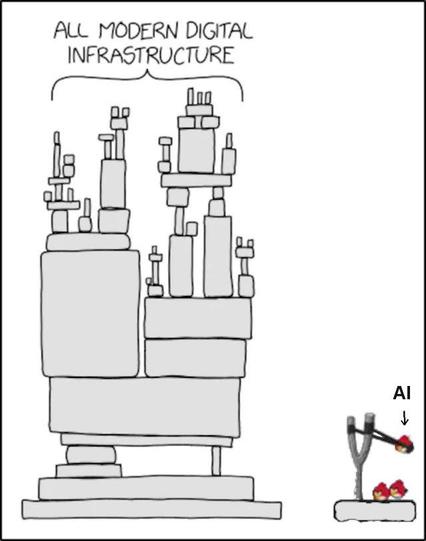
If you look at the NCSC UK too, their remit is to help make the UK the safest place to do business..
but if you look at the general output lately, it’s quantum stuff and firewall espionage stuff. They’re good people but it feels too close to GCHQ, and so too far removed from the operational reality on the ground.
@GossiTheDog we’re in for some chop for sure..
We’ve gone from 3 lines of defence and skills-based hiring to “let the cheapest bidder run our identity service and we’ll cross our fingers that they really do background checks and basic awareness training”
Also, cyber resilience?
We’re seeing teenagers directly skew the UK economy…
Nice work NCSC etc …
When you don’t really know who manages your stuff, grants access to your stuff, backs your stuff up or protects your stuff… you’ve outsourced responsibility whilst remaining entirely accountable
The threat actor ecosystem is largely driven by financial reward… which makes these supply chain watering holes irresistible…