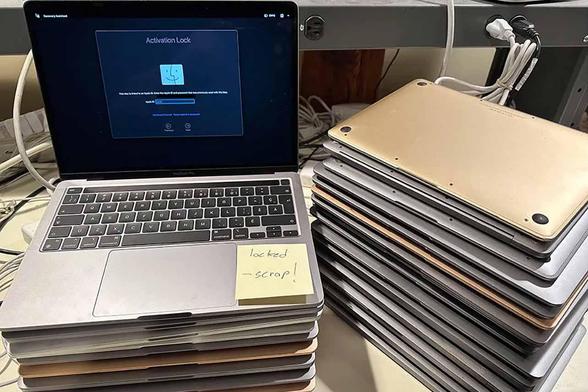
Another reason to hate #Apple We're seeing more 2018+ MacBook Pro/Air donations — but Apple's T2 chip means even after iCloud sign-out and reset, the firmware stays locked to the original account.
Without donor contact, these machines are useless. :(
I've upcycled ~1,000 older Macs, but T2 era machines will end that. It's controlling, creates e-waste, and will only get worse. #righttorepair matters — Apple couldn't care less.