| linktr.ee/investigator515 |
Investigator515
@Investigator_515
- 48 Followers
- 32 Following
- 662 Posts
Open Source Analyst | Investigator | Writer | Crypto | Follow for #OSINT. #Dinsinfomation & #Defense Analysis | SDR Tutorials | Memes
Building Real Skills in RF Security Without a Fancy Lab https://radiohackers.com/building-real-skills-in-rf-security-without-a-fancy-lab-34360782e55d?source=rss----8946e9a3c7a6---4
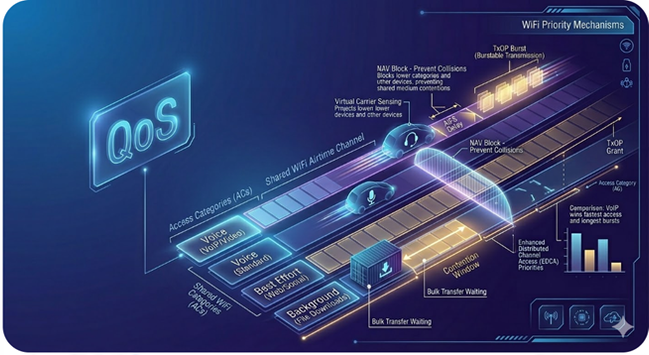
How WiFi QoS Actually Works https://radiohackers.com/how-wifi-qos-actually-works-06c567df2a7e?source=rss----8946e9a3c7a6---4
👀 uh....hello fren? 👀
Bluetooth Security: What Your Devices Are Really Broadcasting https://radiohackers.com/bluetooth-security-what-your-devices-are-really-broadcasting-eef0bce285ca?source=rss----8946e9a3c7a6---4
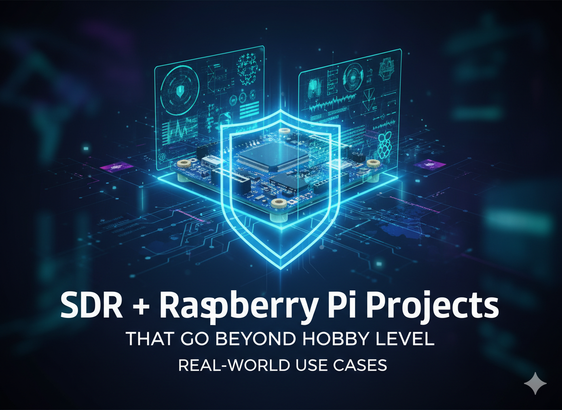
SDR + Raspberry Pi Projects That Go Beyond Hobby Level https://radiohackers.com/sdr-raspberry-pi-projects-that-go-beyond-hobby-level-46a70d75dcd8?source=rss----8946e9a3c7a6---4
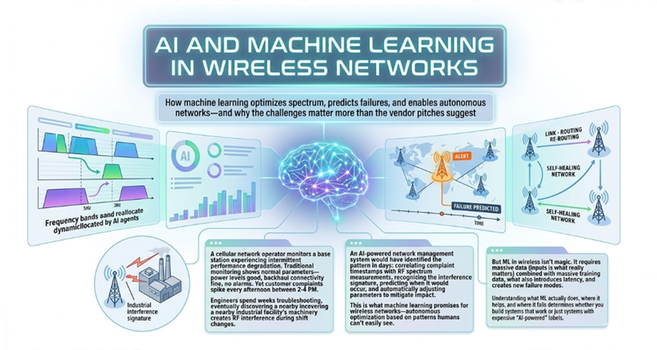
AI and Machine Learning in Wireless Networks https://radiohackers.com/ai-and-machine-learning-in-wireless-networks-c83c736d4f93?source=rss----8946e9a3c7a6---4
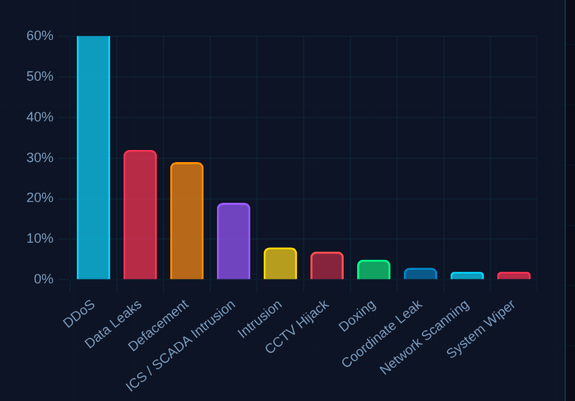
cyber pews go brrrrr
Exploring Bluetooth, ISM, and Wi-Fi Signals with Software-Defined Radio https://radiohackers.com/exploring-bluetooth-ism-and-wi-fi-signals-with-software-defined-radio-2d2aab184de0?source=rss----8946e9a3c7a6---4
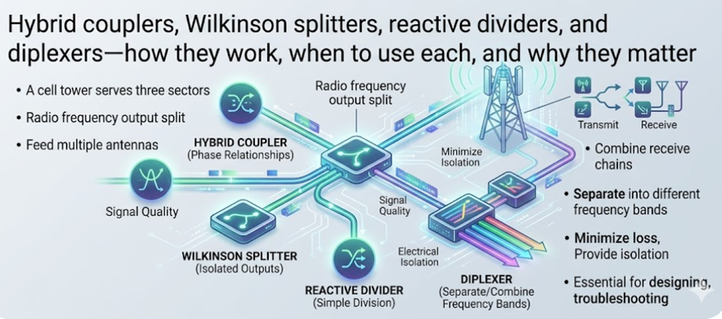
RF Couplers, Splitters, and Diplexers: Components of Wireless Networks https://radiohackers.com/rf-couplers-splitters-and-diplexers-the-hidden-components-of-wireless-networks-0c3280882c83?source=rss----8946e9a3c7a6---4
QoS Over LTE: Redundant Tunnels for Critical Applications https://radiohackers.com/qos-over-lte-redundant-tunnels-for-critical-applications-cb69e8cfa806?source=rss----8946e9a3c7a6---4