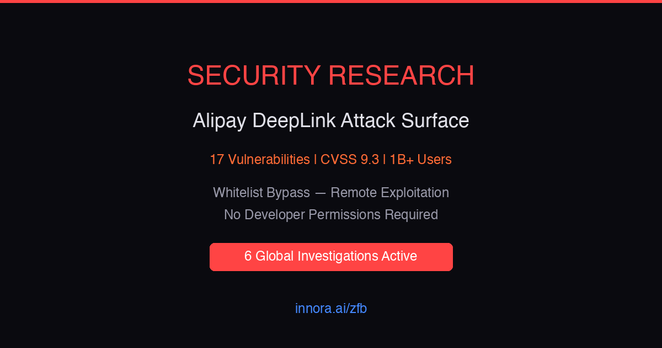
Alipay (100M+ Google Play installs) — what I found by reverse-engineering the APK:
1. A remotely activatable SSL/TLS kill switch
2. 79,371 server-replaceable methods bypassing Play review
3. 1,834 undisclosed data hooks (IMEI, GPS, clipboard, audio)
4. 97% of permission checks return null
Ant Group's response: "these vulnerabilities do not exist."
40 days later, the SSL bypass is still in production.
Thread with code evidence ↓