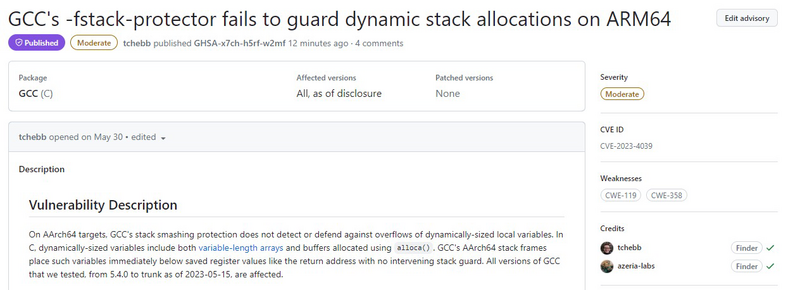
Time for an Arm-twist! CVE-2023-4039
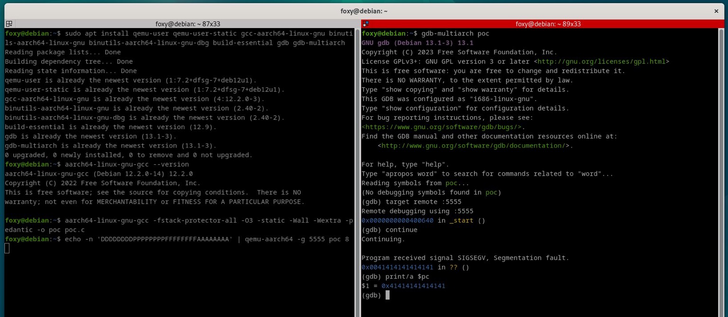
Tom Hebb (Meta red team) and I discovered an 0day in GCC (for AArch64 targets) during my Arm exploitation training.
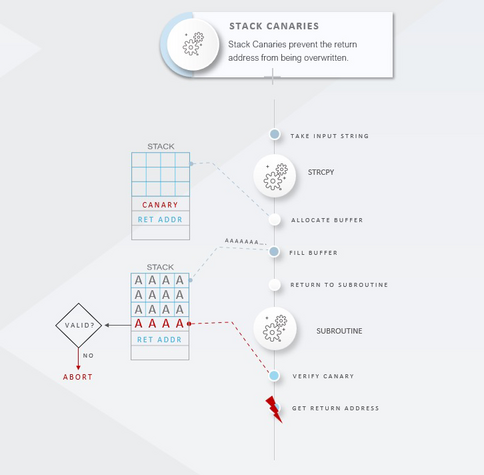
It renders stack canaries against overflows of dynamically-sized variables useless.
https://developer.arm.com/Arm%20Security%20Center/GCC%20Stack%20Protector%20Vulnerability%20AArch64