[🇮🇹 ]😈 Il ransomware Lynx
Lynx si diffonde attraverso molteplici vettori di attacco e, una volta ottenuto l’accesso al sistema, procede a cifrare i file utilizzando l’algoritmo AES, lasciando intatti solo quelli di sistema. Una peculiarità che lo distingue da molte altre varianti è la modalità con cui diffonde la nota di riscatto: Lynx invia il messaggio a tutte le stampanti presenti nella rete, un espediente inusuale che aggiunge ulteriore pressione alla vittima.
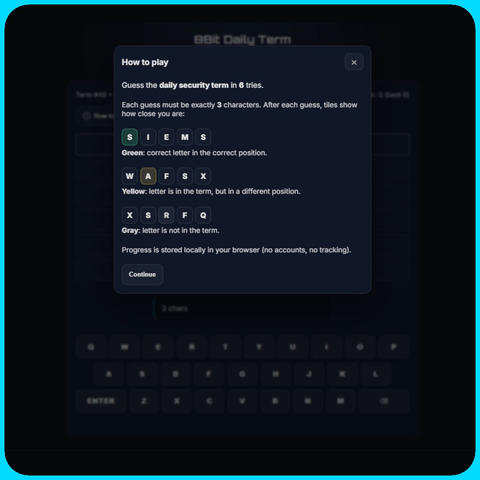
🔗https://blog.8bitsecurity.com/2025/03/24/analisi-approfondita-del-ransomware-lynx/