So, we have a public nginx RCE with demo exploit + a new public Linux LPE with demo exploit, for both of which the patch is less than a day old. So there is a public 0day chain to get root on 50% or so of the internet via a simple HTTP request. Oooooof.
@js CVE-2026-42945 effects the `ngx_http_rewrite_module`, so you're only at risk if you use rewrite and set operations.
@hugo I’d guess most people use rewrites :/
Kevin Beaumont (@[email protected])
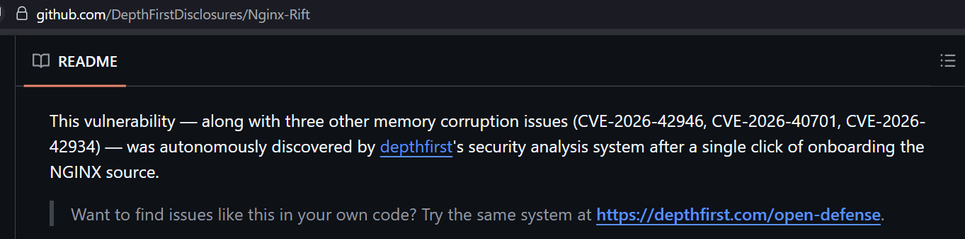
Attached: 2 images CVE-2026-42945 - Nginx (otherwise branded Nginx Rift) It relies on a specific Nginx config to be vulnerable, and for attacker to know or discover the config to exploit it. To reach RCE, also ASLR needs to have been disabled on the box. The PoC they've built specifically disabled ASLR, deploys a specifically vulnerable config and the exploit knows about the vulnerable config endpoint.
