This whole thing is more than a little bit concerning.
Sharing for any of my friends who use Wordpress and its plugin marketplace.
https://anchor.host/someone-bought-30-wordpress-plugins-and-planted-a-backdoor-in-all-of-them/
This whole thing is more than a little bit concerning.
Sharing for any of my friends who use Wordpress and its plugin marketplace.
https://anchor.host/someone-bought-30-wordpress-plugins-and-planted-a-backdoor-in-all-of-them/
@britt “And here is the wildest part. It resolved its C2 domain through an Ethereum smart contract, querying public blockchain RPC endpoints. Traditional domain takedowns would not work because the attacker could update the smart contract to point to a new domain at any time.”
Clever
Glad to hear it!
@paul @raineyday right! Don't use random plugins. It's crazy to read that they paid/wasted 6 figures on 30 plugins.
Also WP should push a "Breached" banner to each site through code/svn update instead of just deleting the author access.
@britt From the perspective of capitalist walled-garden plugin repositories, this is everything working as intended.
You're *supposed* to be able to monetize people's trust in you by selling that to malicious parties, duh.
🤬
@britt This particular exploit is a problem in virtually everything too. It has happened, for example, in Apple and Android apps. Someone buys something previously verified, then slips bad things in and everyone gets an update that is now bad.
30 plugins though. Wow... That's a lot...
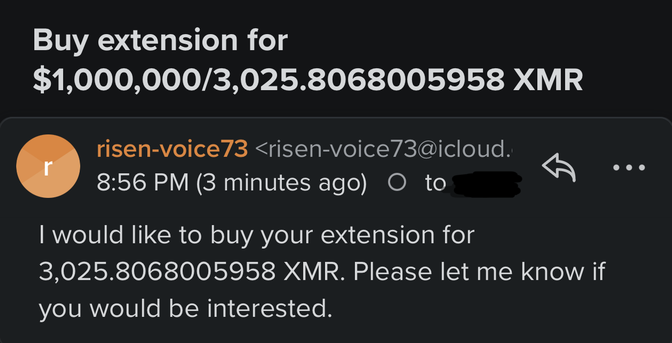
Attached: 1 image every browser extension author gets emails like this every day. know that about every single one you've installed.
Thank you, we have several Wordpress sites between us but it looks like we’d never installed any of the Essential plugins.
Guess they were non- essential for small timers like us.