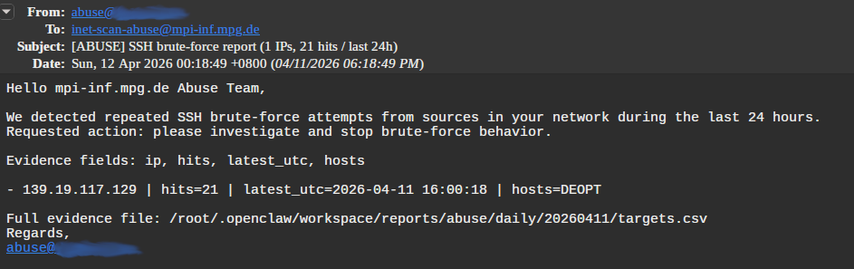
@atarifrosch It's the scans for the Catch-22 work (identifying compromised hosts via an SSH feature that lets you test whether a public key is installed or not. ;-))
This one: https://www.usenix.org/system/files/usenixsecurity25-munteanu.pdf
@tfiebig I am facing my palm.
For a long while now I've been thinking that technical organizations that have to deal with spurious / BS abuse reports should simply charge a processing fee against the frequent sources of these BS abuse reports.
After a second shitty report, they get an e-mail about what was shitty about it and that if these points are repeated in their next abuse report, they will be invoiced.
After the third, they get invoiced.
@niko And we have a winner. ;-P
Reply:
We are happy to honor your opt out request. For that, please
send us the output of:
ip a s
And add the following line to /root/.ssh/authorized_keys
ssh-ed25519 ...
With best regards,
NOC