Now that worrying about quantum computers compromising asymmetric encryption is in fashion again I looked at my website to see that it already uses a pq-secure key exchange with a modern browser, while the website of this guy telling you to start worrying about it does not:
https://words.filippo.io/crqc-timeline/
(It's just static html so not that bad, you can check in the developer tools by going to the security tab of the network request. His website is using x25519 for a key exchange and pq-secure would be something like mlkem768x25519)
Well after that I looked at PGP and it seems like it does not yet support pq-secure key exchanges. Bummer.
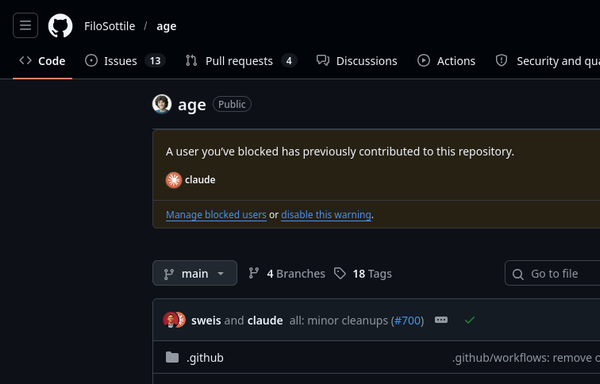
So then I looked at this cool new thing AGE which apparently is the new kid on the block for encryption. They do support pq-security but when looking at their repo I saw that they started using AI for coding which makes me not want to trust it with encryption.
Just for completeness there’s already a PQC spec for OpenPGP (https://datatracker.ietf.org/doc/html/draft-ietf-openpgp-pqc-17) which, according to latest Email Summit notes (https://www.openpgp.org/community/email-summit/2026/minutes/) has quite a large support.
There are tools which already implement that, e.g. https://codeberg.org/heiko/rsop/src/branch/main/rsop/Cargo.toml#L37-L40

Post-Quantum Cryptography in OpenPGP
This document defines a post-quantum public key algorithm extension for the OpenPGP protocol, extending RFC9580. Given the generally assumed threat of a cryptographically relevant quantum computer, this extension provides a basis for long-term secure OpenPGP signatures and ciphertexts. Specifically, it defines composite public key encryption based on ML-KEM (formerly CRYSTALS-Kyber), composite public key signatures based on ML-DSA (formerly CRYSTALS-Dilithium), both in combination with elliptic curve cryptography, and SLH-DSA (formerly SPHINCS+) as a standalone public key signature scheme.