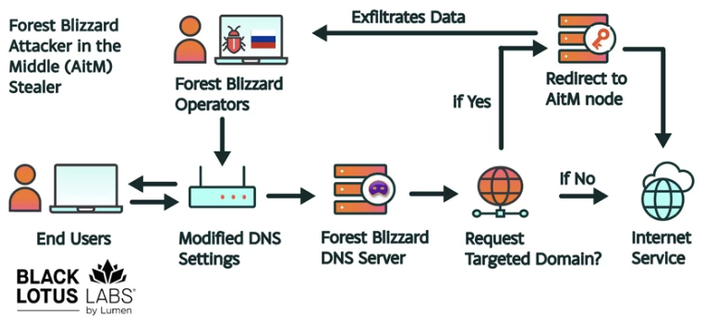
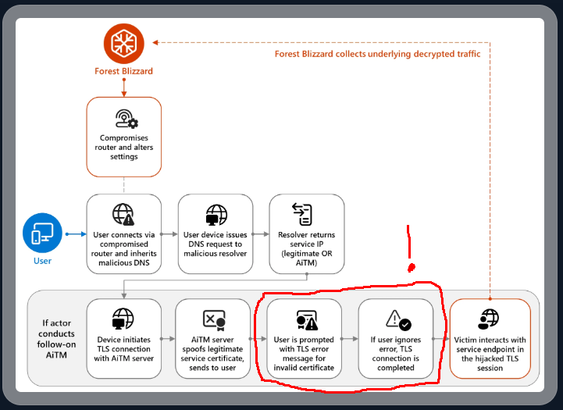
New, from me: Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code.
https://krebsonsecurity.com/2026/04/russia-hacked-routers-to-steal-microsoft-office-tokens/