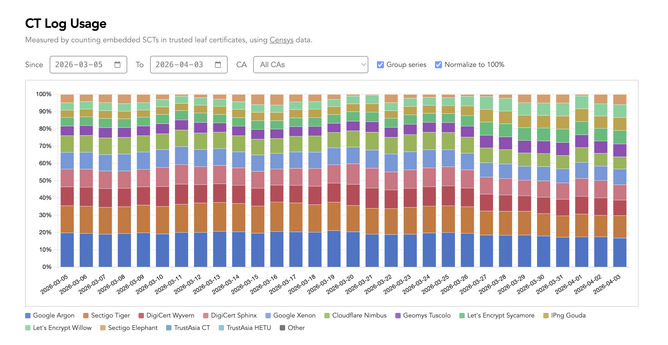
There was no good way to see what CT logs are actually used by CAs, so I made a dashboard of Censys data on exe.dev.
There are some interesting patterns, but the main one is that Let's Encrypt is the only CA that evenly spreads load. Other CAs are mostly using older logs, or their own logs and Google's.
(Of course, LE is 50% of issuance, and GTS is 25%, so the rest don't matter much.)