https://www.internetsociety.org/blog/2026/04/dns-blocking-mind-the-unintended-consequences/
https://www.internetsociety.org/blog/2026/04/dns-blocking-mind-the-unintended-consequences/
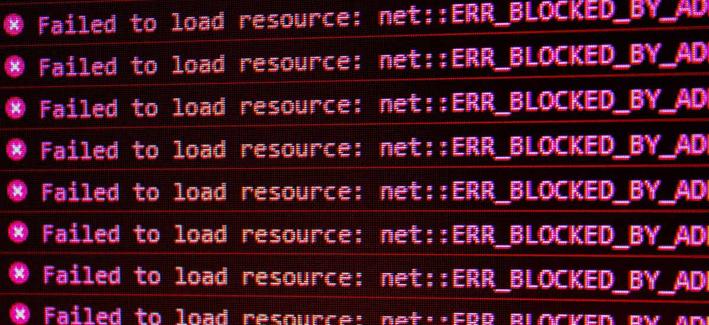
it's not just a blunt/crude tool to do this. it's a mostly ineffective tool. it breaks things way more often than it does what is intended. it's playing russian roulette with 5 bullets and one empty chamber.
an informed choice about who you get to filter your DNS, including making sure it's a well curated and frequently updated block list, can be a feature in your security profile. but the end user must be the one to decide, not some IP/copyright owner on a tear or some politician with as little understanding of security as of brain surgery.
i do blocking in my house but of a very small set of FQDNs. all are known ad brokers or malicious C&Cs. makes browsing vastly faster and i don't miss out on anything. i also do various other things but that blocking is a useful bit. it's definitely not a full solution in any sense. defense in layers.