@j91321
Thanks.
I think at the end of the day, "Product <foo> is vulnerable, but product <bar> mitigates it", does not change the fact that "Product <foo> is vulnerable"
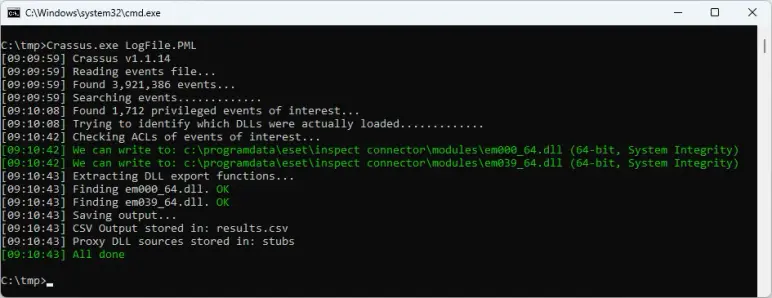
Specifically, in my original analysis, I installed the product with ESET Endpoint Antivirus 11.0.2044.0, and that product does not do anything to mitigate the vulnerability.
I don't know if it's an EEA vs. EES thing, or a version number thing. But either way, it is indeed possible to install ESET Inspect Connector in a way that truly is vulnerable.
Personally, I think that if ESET Inspect Connector contains a vulnerability, then that product itself should get the attention it needs to mitigate it, without relying on another product to mitigate it.