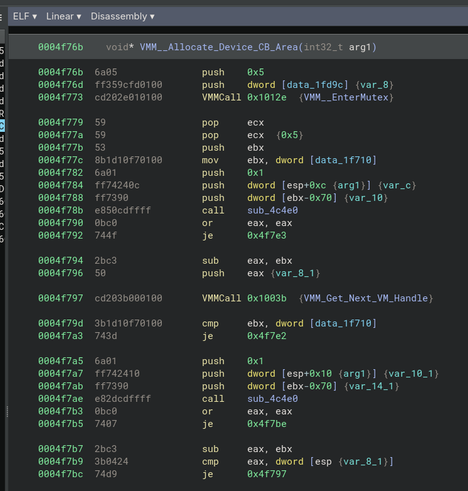
Cooked up a binaryninja plugin that knows how to disassemble VxDCall macros. This is a funky dynamic linking mechanism used in the Windows 9x kernel, it's an int 0x20 followed by an inline dword representing the 16 bit device id and service ordinal which is being called. The kernel patches these sequences with a regular call instruction directly invoking the target service the first time each is executed
@hailey ooo, consumer windows virtual device drivers, that takes me back! 😍