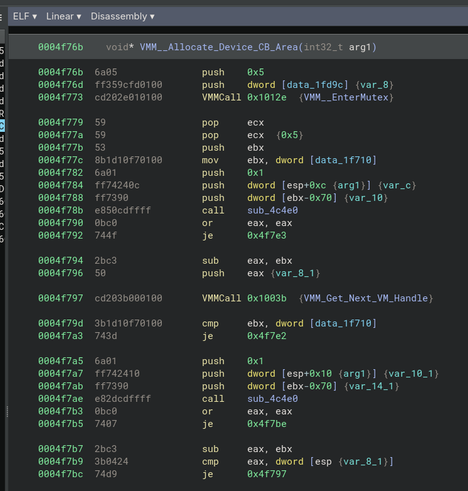
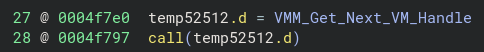
The plugin lifts each VxDCall/VMMCall macro into binaryninja's low-level intermediate language by translating it to two IL instructions: a VxD_Get_Service_Address instrinsic which loads the target address into a temporary, and a plain old call or jump instruction so binaryninja can understand and analyze the branch.
Then, an analysis pass replaces those VxD_Get_Service_Address intrinsics with a direct reference to the resolved service, if the service table was found in the binary being analysed -
And the result is a very readable high-level decompilation! It'll be even better once I transcribe type information from the DDK documentation into a C header file for binaryninja to load!!
plugin's on codeberg, it's in C++ https://codeberg.org/hails/vxdninja