To be clear, I don't have direct evidence or public reporting to corroborate what Troy is saying. I'll keep an eye out and share if and when more information comes to light.
But if you listened to this podcast episode @sawaba and I did on the subject 5 months ago with AJ Yawn, you won't be surprised that what Troy describes has probably been happening to various degrees for a while now: https://www.tenchisecurity.com/en/alice-in-supply-chains/episode-7-hoxz2
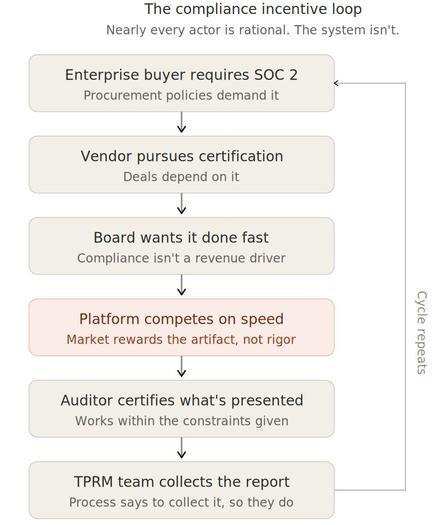
It is worth understanding that "independent" audit reports like SOC 2, even more so than security certifications, have very important economic incentive issues. They give auditees too much control over the process, and are most likely severely overrepresenting how secure third-parties are.
The auditors are chosen and paid for by the third-party, so their economic incentive is not to be thorough, truthful and provide those companies with tough love that leads them to be transparent about (and hopefully improve) their security posture.
The selling pitch and criteria for the auditor and compliance automation vendor selection by a third-party is, overwhelmingly, "we'll make you look good with your customers and close more deals, faster". As the podcast episode makes clear, there are little to no effective processes to desincentivize or punish those providers from misbehaving giving their customers an undeserved clean bill of health.
First parties I talk to give less and less weight to self-assessment questionnaires, trust centers and "independent" audits paid for by the third-party because of that. So the compliance automation and security audit and certification industry is destroying the very value it is promising to provide.
Original LinkedIN post: https://www.linkedin.com/posts/sieira_details-have-emerged-regarding-a-widespread-activity-7415394996184424449-CSzO
UPDATE: https://www.reddit.com/r/soc2/comments/1q7u90o/real_or_fake_the_delve_scandal_or_conspiracy/