I'll take a guess on what the telegram exploit is. Mostly because people seem to be concerned and there is little information and the recommendation appears to be "Disable automatic media download" but I am worried about the mixture of severity and lack of information and at least thought to speculate based on information available and what I can see.
--
Now, please do keep in mind that I have spent like 15mins on this and have hardly done anything serious but hearing "Please do this thing to prevent an exploit but I don't have details" isn't exactly ideal. I'm also jumping to some conclusions as what is exploitable
--
1. Got notified regarding to this CVE via a friend.
* CVE for Telegram - https://bsky.app/profile/redteef.bsky.social/post/3mi3ki5tip227
The main advice appears to be disable automatic media download - My assumption is that some library related to processing media appears to have some issue.
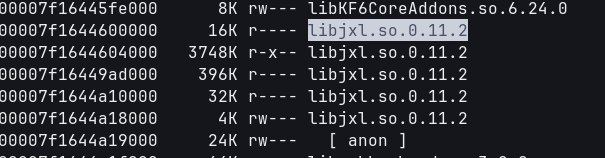
2. pmap of my running telegram process - Saw libjxl and wondered what state it was in (Refer to media attached)
3. Looked up issues related to libjxl on github - https://github.com/libjxl/libjxl/issues/4539
and https://github.com/libjxl/libjxl/issues/4539
"ibjxl JPEG XL decoder crash due to uninitialized pointer access in malformed images" - One of the screenshots output "Illegal Instruction (Core Dump)" which is sinister, this can include the CPU attempting to execute an instruction it doesn't understand and if that segment can be manipulated, this can potentially lead to arbitrary code execution.
Which then also lead me to this: https://github.com/advisories/GHSA-76gx-97cq-65f5
---
Disclaimer: I can't say it is even about libjxl or related to the CVE mentioned in 1 but I can at least see an attack like so: (which gives weight to disabling media for telegram).
1. Attacker crafts a suitable image to manipulate the decoder, image contains data that can either manipulate the pointer and/or data that the segment it could point to (for reference, just enough data to get a shell or establish a connection to something else is enough)
2. Attacker sends the image on a platform where the user using this library can then decode it.
3. The image that is decoded will then be able to execute the payload - Attacker could gain control via this method.
---
While this may seem silly but please also do not hound or abuse the devs at libjxl. Last thing I want are people who are trying to do their best to fix the issues I have listed and do not control what telegram includes in their builds.