The result of a cryptographic transformation of data that, when properly implemented, provides a mechanism to verify origin authenticity and data integrity and to enforce signatory non-repudiation.
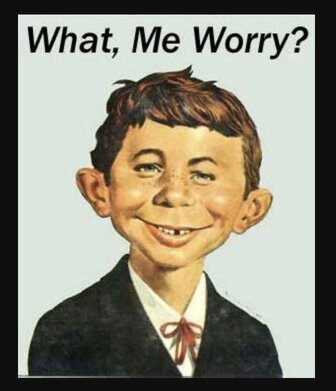
"when properly implemented". psh yeah you can do cryptographic transformation of data, but can you provide a mechanism to verify origin authenticity and data integrity and to enforce signatory non-repudiation?????