The open source vulnerability scanner trivy has experienced a *second* security incident: a compromised release (v0.69.4) was published to the trivy repository.
https://www.stepsecurity.io/blog/trivy-compromised-a-second-time---malicious-v0-69-4-release
Trivy Compromised a Second Time - Malicious v0.69.4 Release, aquasecurity/setup-trivy, aquasecurity/trivy-action GitHub Actions Compromised - StepSecurity
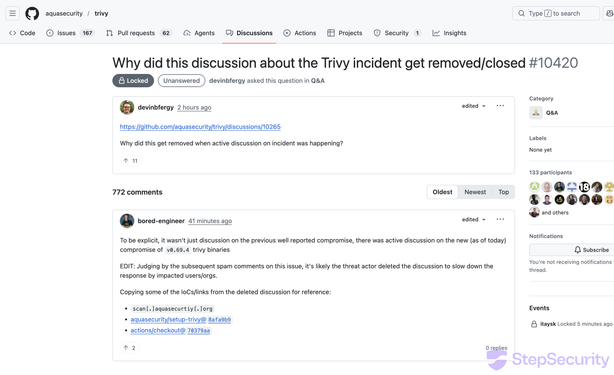
On March 19, 2026, trivy — a widely used open source vulnerability scanner maintained by Aqua Security — experienced a second security incident. Three weeks after the hackerbot-claw incident on February 28 that resulted in a repository takeover, a new compromised release (v0.69.4) was published to the trivy repository. The original incident disclosure discussion (#10265) was also deleted during this period, and version tags on the aquasecurity/setup-trivy GitHub Action were removed. Trivy maintainers deleted the v0.69.4 tag and Homebrew downgraded to v0.69.3. The following is a factual account of what we observed through public GitHub data.