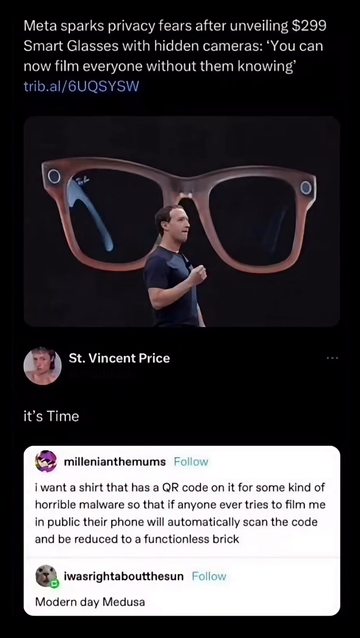
Dumb glasses
That sort of exists:
en.wikipedia.org/wiki/EICAR_test_file
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*That’s just a test file tho. Its whole purpose is to prove heuristic based scans work.
It’s not actually a virus.
No it’s not but the whole point of it is that antivirus packages detect it, and they will kill and quarantine the process handling the data. Its purpose is to trigger an antivirus response for testing purposes.
So it can indeed be used as a DoS kinda thing in many cases.
There’s some AV packages like Lookout that are pretty common in corporate environments.
And really any big data collection through apps will make itself to servers eventually if course. You don’t need to open a URL for this to trigger, the eicar code being in memory of a process is enough.
Of course you do need to decode the QR. But I’m sure many environments focused on video data collection would device QR codes.
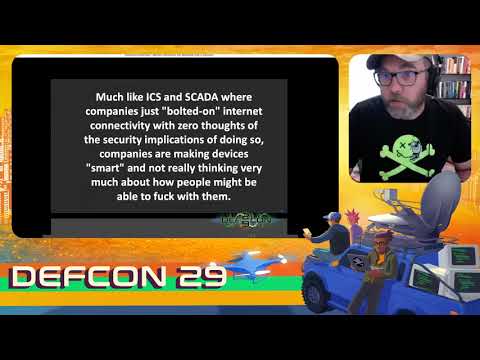
Yeah, turns out a lot of companies don’t really think about security, here’s a DEF CON talk where they find stuff that chokes on it: